What is a VPN? How it Works & How to Use a VPN (2024)
Short for Virtual Private Network, a VPN creates a secure, anonymous connection between you and the internet so that your activities and location details are hidden. Since no one can see what you’re doing online when using a VPN, they are also an essential tool in places where online censorship limits your internet access.
While they can seem technical and difficult, you don’t need to be an expert to understand what a VPN is, what it does, and why you should use one. In this guide, you can learn everything you need to know about VPNs — from how they work to how to choose the best one for you.
There are plenty of beginner-friendly VPNs, but my personal favorite is ExpressVPN. Despite being packed with quality security features, its apps are very simple to use. It’s also backed by a 30-day money-back guarantee so you can try it risk-free. If you’re not totally sold in that time, you can claim a full refund.
What is a VPN and How Do VPNs Work?
A VPN is an essential security tool that adds a layer of protection to your online connections. Without a VPN, your internet activity can be easily intercepted and viewed by others. This includes your browsing history, downloaded files, online banking details, and passwords.
It’s possible for third parties to see what you’re doing because all your activities are linked to your device through your Internet Protocol (IP) address. Your IP address reveals your physical location and can be used to track you down. It’s like sending postcards through the mail — anyone can read the message and see your name and address.
But when you’re connected to a VPN, your internet activity is encrypted, and your real IP address is masked. No one can see who you are or what you’re doing. Some VPNs even use server obfuscation to disguise your traffic, making it difficult for sites and services to detect that you’re using a VPN.
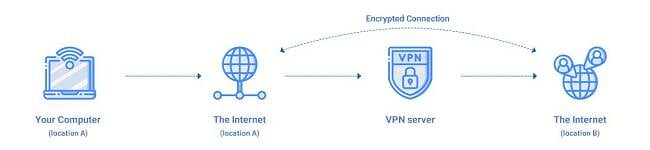
With a VPN, you’re sending highly secure private messages that only the intended recipient can access. These messages contain no sender information, ensuring anonymity. If anyone tries to snoop on the message, they will only encounter a scrambled mess of encrypted data.
Additionally, when you use a VPN, the website or service you are accessing sees the VPN server as the source of your data, providing you with the freedom to explore the internet without any network limitations.
Do You Really Need a VPN?
Yes, you need a VPN to safely and freely access the internet. Here’s a list of reasons why consumers currently use VPNs:
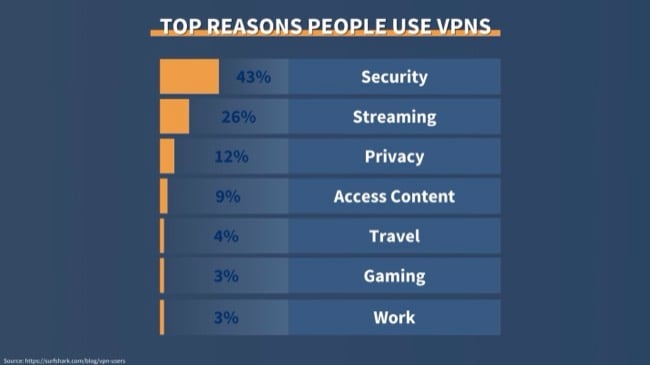
Let’s take a closer look at some of the most popular reasons for using a VPN and how the VPN works to enhance safety and improve your online experience.
Secure Your Online Privacy
Some networks like free public WiFi and hotspots are not secure. It’s so easy to intercept another person’s device when it’s connected to the same network. Since hackers know this, they usually watch these networks for easy targets to steal important information from — like your credit card details.
Governments and your ISP can also monitor your online activities, but a VPN can encrypt your traffic for privacy and security.
Bypass Blocks, Restrictions, Censorship, and Firewalls
Network blocks occur in various forms:
- Government censorship: Many countries around the world censor the internet because certain content doesn’t align with local political or religious beliefs.
- Network restrictions: Local administrators for networks like schools and offices block access to sites and services that aren’t considered appropriate.
- Location restrictions: Some online services (like Hulu and BBC iPlayer) impose restrictions depending on your geographical location to avoid copyright issues.
If you’re experiencing restrictions like these, you can use a VPN to provide access to the online content you want to see. However, you should know it’s against most streaming platforms’ Terms of Service to use a VPN to bypass geo-blocks meant to protect their licensing agreements. Since this can amount to copyright infringement, I don’t condone using a VPN in this instance.
In countries with government censorship, a VPN can overcome internet restrictions like China’s Great Firewall. It’s important to note that there can be severe legal consequences for doing this, since VPNs can also be banned in countries with strict online censorship. No tourist have ever been penalized for using a VPN to access their usual content, though. Otherwise, simple tasks like Googling or updating your status on Facebook are impossible.
You can also use a VPN to connect to different game servers, letting you play online games like Call of Duty: Warzone with friends in other countries.
Torrent Files Safely and Anonymously
Torrenting is risky since P2P connections expose your true location to every peer connected to the same file, making you vulnerable to hackers and identity theft. You can also never be sure if your downloaded files are 100% safe.
Since VPNs hide your IP address and include many other security features, you’re safe from malicious P2P users. Plus, your ISP won’t be able to see that you’re torrenting, so you’re less likely to experience bandwidth throttling if you download frequently.
A VPN like CyberGhost provides dedicated torrenting servers to keep your download speeds fast, your file-sharing anonymous, and your devices protected from malware.
Improve Your Internet Connection and Speeds
At times, your ISP may deliberately slow down your Internet connection (if it’s legally allowed to do so). This could be because your ISP detects your torrent or streaming activity, or because you’ve gone over a certain data limit. Some ISPs even use this strategy to get you to upgrade your connection. The practice is known as “throttling.”
With a VPN, your activity remains private so your ISP can’t see what you’re doing to throttle your connection. This means you may actually see an increase in speeds.
Are VPNs Safe? How to Choose a Secure VPN in 2024
It’s not always obvious which VPN features are marketing gimmicks and which are truly useful. As someone who uses VPNs extensively, I’ve compiled a list of the critical features that you should keep in mind when selecting a VPN.
Strong Encryption and Connection Protocols
One of the main reasons for using a VPN is to make your connections safe, so don’t skimp when it comes to security. Look for a service with 256-bit AES encryption — the industry standard — and secure protocols like OpenVPN and WireGuard.
Some VPNs also use their own protocols. ExpressVPN has a proprietary Lightway protocol as its default connection, optimized for fast speeds and strong security.
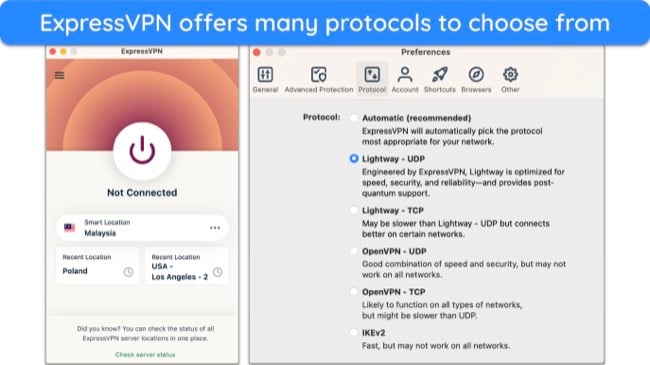
The VPN protocol you choose depends on how much security and speed you need, as well as your device. Below are the most common protocols:
- OpenVPN: Popular open-source protocol that’s supported by nearly all VPNs. It’s the most secure protocol available with no known weaknesses.
- WireGuard: Open-source protocol with fewer lines of code than OpenVPN, so it’s easier to audit for security vulnerabilities. It balances speed and security at the same time.
- IKEv2: Fast, secure, and popular with mobile users. The biggest drawback is that it’s not open-source and can’t be audited.
- SSTP: Less popular protocol that works mostly on Windows. Good for bypassing firewalls but speeds are average.
- L2TP/IPSec: Mostly used on iPhones, although it’s outdated so you should avoid it where possible.
- PPTP: PPTP isn’t secure and has been previously cracked by the NSA in the US.
Strict Zero-Log Privacy Policy
It’s important to choose a provider with a no-log policy that has been independently audited and verified. Otherwise, the VPN could be storing data relating to your online activity and sharing it with third parties, like advertisers or government bodies.
Even when a VPN claims to keep “zero logs,” read the fine print in the privacy policy. You’ll likely find that many VPNs record your IP address, bandwidth usage, payment details, and connection timestamps. However, the best VPNs won’t store any identifying data. This means none of your online activity while connected to the VPN can be linked to your personal information.
A VPN like ExpressVPN not only has an audited no-log policy, but also a strong track record. In 2017, the Turkish government demanded user logs from ExpressVPN to aid a criminal investigation. When the authorities physically seized a server, no identifying customer data was found.
Also, make sure the provider is based outside the 5/9/14 Eyes alliances (these are groups of countries that share surveillance data). If you’re not sure where a provider stands, read the privacy policy.
Fast Speeds
Using a VPN can slow down your connection, as your data is being encrypted and routed through another server. With some VPNs, the difference is barely noticeable, whereas others can cause a considerable slowdown. The best VPNs can mitigate the speed loss caused by encryption, ensuring your speeds stay fast on every connection.
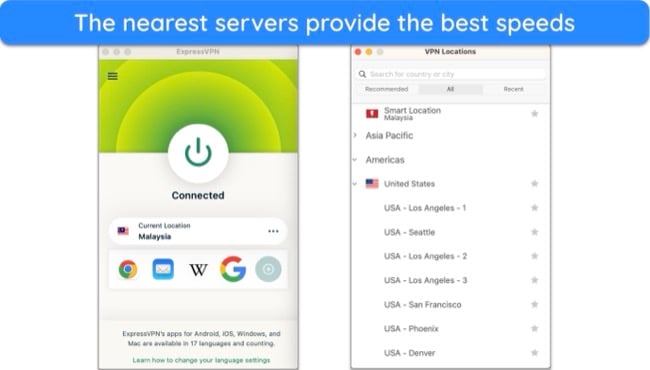
VPNs with a lot of servers can reduce overcrowding to perform at an optimal level. You’re also more likely to find a local connection, which will have a smaller impact on your speed. Generally, the further away the server is, the slower your internet because it will take longer for your data to get there.
Works With Streaming Services, Torrenting, Gaming, and More
VPNs allow you to access the internet without restrictions. By masking your true location, you can torrent public domain content and access your usual online services, even if you’re in a country where these aren’t available. However, many VPNs are easily blocked by VPN detection technology — streaming services often block VPN IP addresses to protect their copyright agreements.
If you want to use your VPN to watch Netflix in the US locally or get through a certain country’s firewall, find out first if it’s capable. Many VPNs have details on their support sites, letting you know which services they work with and whether they can get around tough restrictions.
You can also use their free trials and money-back guarantees to test VPNs. However, even the best VPNs can’t always avoid detection, but with regular server updates and IP refreshing, you’ll soon find a working connection.
Supports Multiple Devices and Platforms
Top-tier VPNs have native apps for popular platforms, including Windows, Mac, Android, iOS, and Linux devices. You’ll also find VPN support for smart TVs, Amazon Fire devices, Roku, Kodi, routers, Chromecast, and other devices that don’t support VPNs directly (like gaming consoles). Before subscribing to your VPN, make sure that it works with the devices you want to secure.
If you choose a provider that allows several simultaneous connections, you don’t have to worry about which devices are protected. You can stay signed in to your VPN without getting logged out for exceeding the limit.
24/7 Customer Support
If something goes wrong or you have questions, you need to be confident that you’ll get a fast response from your VPN provider. Choose a service with 24/7 live chat, email support and a comprehensive website with FAQs, troubleshooting, and setup guides. It’s even better if your VPN has step-by-step video guides.
Value for Money
You don’t necessarily have to choose the cheapest VPN to get your money’s worth. Instead, look for a service that offers all the features mentioned above at a reasonable price. Usually, this means subscribing to a long-term plan to get the best value. However, VPNs often have discount codes and coupons so you can get a great deal on any subscription plan.
Also, many VPNs offer money-back guarantees. This lets you fully test the service to make sure it’s right for you — if you change your mind or aren’t totally happy, you can get a full refund.
Are There Disadvantages to Using a VPN?
No VPN is perfect, so there are some potential disadvantages you should be aware of — fortunately, these can be minimized or even eliminated by using one of the top VPNs in 2024.
- You may notice a slight connection speed slowdown. Your data takes longer to travel due to the encryption and additional server routing. However, top VPNs mitigate speed loss so effectively that you won’t notice a difference.
- Your data can still leak. If your VPN connection is unexpectedly interrupted, your online activity and personal data (like your IP address) can be exposed. So, make sure your VPN has an active kill switch to prevent these kinds of leaks.
- VPNs won’t keep you completely anonymous. Web trackers, cookies, and browser fingerprinting can be used to identify you. They store and reveal which websites you visit, your general location, and more. You’re also identifiable if you log into a service like Google, or YouTube with a VPN as your activities can still be traced back to your account.
- Shady VPNs can log and sell your data. Many completely free VPNs profit by logging and selling your data to third-party advertisers or worse, hackers. Check your VPN’s privacy policy and only subscribe to a reliable, trustworthy service.
- Not every server will work every time. Services like Netflix and Disney+ have powerful VPN detection technology that can block your VPN connection. Fortunately, top VPNs have optimized servers that are regularly tested and refreshed to guarantee a working connection.
- The best VPNs aren’t free. To get optimal security, you’ll have to pay for a subscription. However, this doesn’t mean your VPN has to be expensive. Longer subscriptions are almost always better value, but if you’re on a budget you can also get a quality VPN at an affordable monthly price.
- VPNs aren’t legal to use worldwide. Some countries, like China, Russia, Turkey, and Iraq, heavily restrict or even ban the use of non-government-approved VPNs. If you plan on visiting one of these countries, it’s a good idea to download your VPN before you arrive and make sure you’re aware of local laws and regulations before you connect.
How Much Do VPNs Cost?
There are multiple factors to consider when looking at the cost of a VPN:
- The VPN itself — well-known and tested services usually cost more.
- The length of the VPN subscription.
- The number of servers, including specialized servers (for streaming, torrenting, and gaming).
- Extra features, like split tunneling, ad and malware blockers, server obfuscation, and more.
On average, a VPN will cost around $6-7 per month. Very rarely will you find a VPN charging more than $10 per month, and you can definitely find a better service at a lower price. Plus, you’ll always get a more cost-effective deal when you choose a long-term subscription versus a short-term or month-to-month plan.
The price of VPNs varies between services — for comparison, ExpressVPN’s lowest price plan is $6.67 per month for a subscription, while Private Internet Access’s monthly cost for its plan is just $2.03/month. However, price isn’t the only thing to consider and this depends on what you need a VPN for primarily.
Free VPN vs. Paid VPN: Which Is Better?
Premium VPNs offer top-tier security with extra features — you won’t get the same level of protection with a free service. There are free VPNs owned by premium services that are safe, but they’re extremely limited. These “freemium” services often limit how much data you can use, the number of servers you can connect to, and the speed.
It’s expensive to run a VPN network, and the company still needs to make money even if you’re not paying. That’s why many free VPNs are scams meant to collect and sell your data, spam you with annoying popup ads, or even trick you into downloading malware. To be safe, it’s always better to get a premium VPN than a free one. Or at the very least a freemium VPN that’s supported by paid subscribers.
The Best VPNs in 2024 for Beginners — Full Test Results
1. ExpressVPN — Best VPN for Beginners With Excellent Security Features and Pre-Configured Settings
Key Features:
- Global network of 3,000+ servers in 105 countries to connect from anywhere
- Military-grade encryption, data leak protection, kill switch, and server obfuscation secure your data
- Connect 8 devices simultaneously
- 24/7 customer support with live chat, email, FAQs, and setup guides
- 30-day money-back guarantee on all plans
ExpressVPN’s apps are the easiest for beginners to start using a VPN. They’re pre-configured for top security and privacy, so you don’t need to make changes manually — simply log in, hit the power button, and you’ll be automatically connected to the best server near you.
Besides the standard AES-256-bit encryption that’s a must for all VPNs, ExpressVPN has a few other features like Advanced Protection. Alongside blocking ads and trackers, it works like a parental control setting that stops malicious and adult sites from loading. These are not turned on by default to suit your online preferences, but it’s as easy as checking a few boxes.
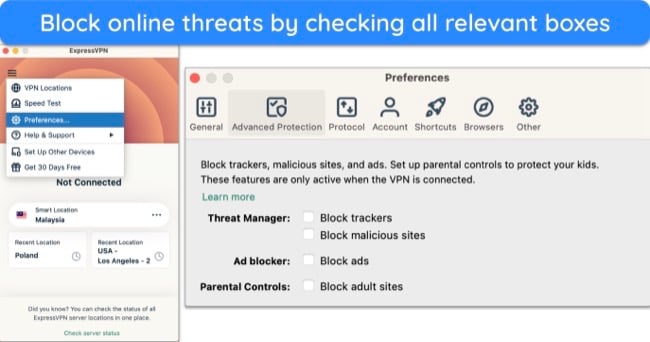
Other pre-configured features that ExpressVPN has to protect your identity online include:
- Data leak protection — protected all my connections against DNS, IPv4, IPv6, and WebRTC leaks.
- Network Lock kill switch — blocks access to the internet if the VPN connection is unexpectedly interrupted.
- Server obfuscation — masks VPN traffic to look like regular traffic, avoiding VPN detection technologies that could block your access to certain sites.
- TrustedServer technology — RAM-based servers can’t physically log or store your data, and they’re wiped clean during reboots.
- Privacy-friendly jurisdiction — based in the British Virgin Islands that’s not a part of any internet surveillance data-sharing alliance.
Among all the VPNs I tested, ExpressVPN gave me the fastest speeds. Although distant servers usually slow down connections, I saw a tiny drop in speed when I tested a server 4,000 miles away from me. As a result, high-bandwidth activities didn’t take much longer than usual and I could watch YouTube videos without lag or dips in quality.
It’s a little more expensive than other services, with plans starting at $6.67 per month for a subscription. However, ExpressVPN’s security, speeds, and reliability make it well worth the price.
If you decide to try ExpressVPN, it’s risk-free — all plans are backed by a 30-day money-back guarantee. I tested the policy by canceling my ExpressVPN account via 24/7 live chat. My refund request was approved in under 5 minutes with no questions asked. Best of all, I had the full amount in my account in less than 5 business days.
ExpressVPN works with: Netflix, Disney+, Max, Hulu, Amazon Prime Video, BBC iPlayer, ITVx, ESPN, DAZN, Peacock TV, Sling TV, fuboTV, Paramount+, Sky Go, Crunchyroll, and more.
ExpressVPN is compatible with: Windows, macOS, Linux, Chromebook, Android, iOS, Chrome, Firefox, Edge, PlayStation, Xbox, Amazon Fire TV, Amazon Fire TV Stick, Chromecast, Roku, Android TVs, smart TVs, routers, and more.
2024 Update! ExpressVPN has dropped prices for a limited time to a crazy $6.67 per month for the 1-year plan + 3 months free (you can save up to 49%)! This is a limited offer so be sure to grab it now before it's gone. See more information on this offer here.
2. CyberGhost — Optimized Servers Worldwide for Streaming, Torrenting, and Gaming
Key Features:
- 11,800+ servers in 100 countries with a huge optimized selection
- Military-grade encryption, data leak protection, kill switch, and WiFi protection
- Protect up to 7 devices at once
- 24/7 customer support with live chat, online ticket, and setup guides
- 45-day money-back guarantee on all long-term plans
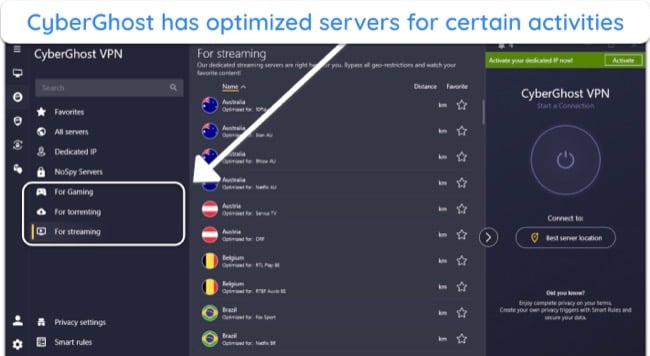
CyberGhost has optimized servers to easily connect to the best server for your activity. The optimized streaming, torrenting, and (Windows-only) gaming servers are available worldwide and tested regularly so that you get a reliable and smooth connection every time. Other servers work for these activities as well, but you’ll get the best performance with these.
One of CyberGhost’s top advanced features is WiFi protection, which is ideal if you use public WiFi frequently. You can set up the VPN to connect immediately when your device detects a WiFi network. This will ensure you don’t accidentally share sensitive data without first securing your connection. CyberGhost also has:
- Malware blocker — prevents ads and pop ups that link to malicious sites from loading.
- NoSpy servers — owned and maintained by CyberGhost in its headquarters in Romania to prevent interference by third-party data center operators.
- Dedicated IP address — provides your own IP address to bypass CAPTCHAs, work remotely, and avoid IP blacklisting due to other users’ behavior (available for an extra fee).
- Security suite for Windows — includes an antivirus program, limits data collection by Microsoft, and updates outdated apps for security.
During speed tests, CyberGhost was slightly slower than ExpressVPN. However, all 19 servers I tested locally and within 2,000 miles were fast enough to make smooth video calls. If you plan to stream, torrent, or play online games, choose the optimized servers if they’re available in your location as they’re faster than the regular ones.
The only thing I didn’t like is that the money-back guarantee for CyberGhost’s monthly plan is only for 14 days. This wasn’t long enough for me to thoroughly test all of its features. Fortunately, all long-term plans come with one of the longest refund periods — 45 days.
I recommend the 2-year + 4 months plan for this reason and because it only costs $2.03/month. After contacting a support agent via 24/7 live chat, I arranged my refund without hassle and had my money back in less than a week.
CyberGhost works with: Netflix, Disney+, Max, Hulu, Amazon Prime Video, BBC iPlayer, ITVx, ESPN, DAZN, Peacock TV, Sling TV, Sky Go, Crunchyroll, and more.
CyberGhost works on: Windows, macOS, Linux, Android, iOS, Chrome, PlayStation, Amazon Fire TV, Amazon Fire TV Stick, Chromecast, Android TVs, smart TVs, routers, and more.
2024 Update! You can subscribe to CyberGhost for as low as $2.03 per month + get an extra 4 months free with the 2-year plan (save up to 84%)! This is a limited offer so grab it now before it's gone. See more information on this offer here.
3. Private Internet Access (PIA) — Customizable Security Settings to Suit Your Online Activities
Key Features:
- Massive global network of 35,000+ servers in 91 countries
- Flexible encryption, data leak protection, kill switch, and MACE ad, tracker, and malware blocker
- Secures unlimited devices simultaneously
- 24/7 live chat and email support, plus online guides
- 30-day money-back guarantee
PIA’s security features are easy to use and highly flexible so it’s ideal for beginners and advanced VPN users. If you’re not sure what to choose or if you don’t know what a feature does, just hover over the “i” icon and you’ll have more details.
Some of PIA’s features that beginners can explore are:
- Kill switch — use the VPN Kill Switch to prevent access to the internet when the VPN connection is interrupted, or the Advanced Kill Switch that prevents leaks even when the VPN is off.
- Protocols — switch to the WireGuard protocol from OpenVPN if you want both a secure and high-speed connection.
- Encryption standard — try OpenVPN’s 256-bit encryption instead of the default 128-bit for maximum security when transacting online — ideal when using public WiFi or unsecured networks.
Compared to other VPNs, PIA has an enormous network of 35,000+ servers in 91 countries, so you should be able to find a server near you easily. Although it’s not clear how many servers are in each location, I didn’t have trouble connecting to all 23 PIA servers I tried — I didn’t experience issues or slowdown due to congestion.
When I tested PIA’s local servers, there was only a slight decrease in my baseline speeds. My connection was consistently fast enough to watch Netflix content in UHD without lag. Lowering the encryption back to 128-bit or switching to the WireGuard protocol also improved my speeds.
The only downside is that all these customizations and options might be a bit overwhelming for beginners at first. While the advanced features are worth trying as you get used to the apps, there are other VPNs that are simpler to set up or come configured automatically.
Overall, PIA is a solid choice for online security, and it’s one of the lowest-priced VPNs. Plans start at $2.03/month, which is hard to beat. Plus, the service is backed by a 30-day money-back guarantee. I got my money back in just 6 days after contacting support via live chat.
PIA works with: Netflix, Disney+, Max, Hulu, Amazon Prime Video, BBC iPlayer, ITVx, ESPN, Peacock TV, Sling TV, Crunchyroll, and more.
PIA works on: Windows, macOS, Linux, Android, iOS, Chrome, Firefox, PlayStation 4, Amazon Fire TV devices, Apple TV, smart TVs, routers, and more.
2024 Update! You can subscribe to PIA for as low as $2.03 per month + get an extra 4 months free with the 2-year plan (save up to 83%)! This is a limited offer, so grab it now before it's gone! See more information on this offer here!
4. NordVPN — Specialty Servers for Multiple Functions Make it an Easy Option for Beginners
Key Features:
- Network of 6,300+ servers in 110 countries
- AES 256-bit encryption, Double VPN, kill switch, and Threat Protection
- Use up to 10 devices at the same time
- 24/7 live chat, email support, and online tutorials
- 30-day money-back guarantee
Like CyberGhost, NordVPN has specialty servers optimized for different functionalities. The Onion Over VPN servers allow you to use any regular browser to access the Tor network, while its double VPN routes your traffic through 2 servers for double encryption and extra security. NordVPN also has 5,000+ P2P servers worldwide and an obfuscated network across 16 countries.
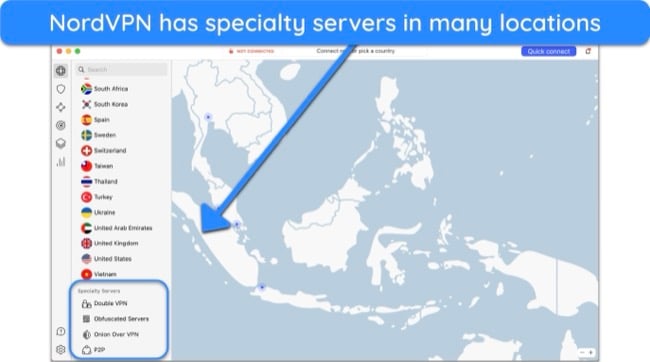
NordVPN’s Meshnet connects all your devices so that you can share files in an encrypted tunnel. You can access your home desktop remotely from your computer at work to retrieve important files. NordVPN has plenty of resources online to explain what and how to use Meshnet for beginners.
The VPN includes all the common security features including military-grade encryption, a kill switch, as well as data leak protection. Beyond that, NordVPN also offers Threat Protection to block risky websites and apps, stop web trackers, and remove annoying ads. It also automatically scans downloaded files and removes malware.
One thing to remember is that NordVPN’s user interface can be difficult to navigate. Besides the distracting map, certain settings can be difficult to find. If it’s your first time using NordVPN, give yourself some time to get used to the apps.
If you want to get NordVPN, the 2-year + 3 months plan is $3.09 a month. If you don’t like it, you can ask for a refund with its 30-day money-back guarantee. When I tested it, a live chat agent processed my request immediately. The money was back in my account 5 days later. Just remember that NordVPN’s prices increase more than 50% after your initial contract expires.
NordVPN works with: Netflix, Disney+, Max, Hulu, Amazon Prime Video, BBC iPlayer, Peacock TV, Sling TV, Crunchyroll, and more.
NordVPN works on: Windows, macOS, Linux, Android, iOS, Chrome, PlayStation 4, Amazon Fire TV devices, smart TVs, routers, and more.
5. Surfshark — Rich With Easy-to-Use Features That are Important for New Users
Key Features:
- 3,200+ servers in 100 countries
- Military-grade encryption, IP Rotator, data leak protection, and kill switch
- Allows unlimited device connections
- 24/7 live chat, email support, online guides
- 30-day money-back guarantee
Surfshark has many advanced features that can benefit beginners. For example, the IP Rotator changes your IP address frequently to make it difficult for others to trace you based on your online activities. There’s also a built-in speed testing tool that you can use to connect to the fastest server, and CleanWeb is great for blocking ads and malicious websites.
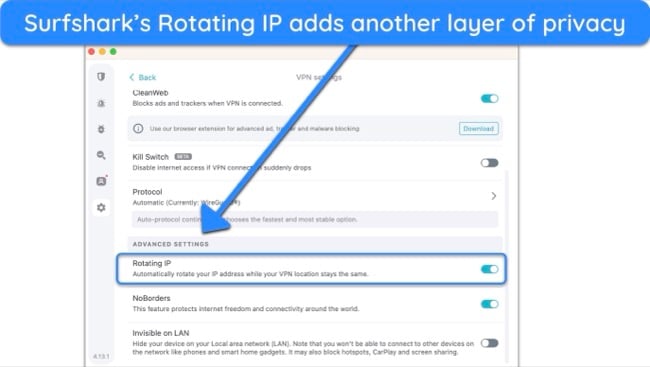
Surfshark also offers double encryption with its Dynamic MultiHop feature. Unlike other VPNs where you can only select one of the servers, Surfshark allows you to select both. This can be useful to improve speed, as double encryption connections are slow. For most people, single encryption is strong enough, but if you need it, it’s easy to use with Surfshark’s intuitive apps.
Unfortunately, Surfshark is quite slow on distant servers with shows buffering once or twice within a 1-hour period. However, Surfshark’s servers within 2,000 miles were really fast. The servers in my location affected my baseline speeds by 32% on average but it was still fast enough to watch YouTube videos without any lags.
If you want to try Surfshark, the 2-year + 2 months plan is the best at $2.29 a month. All its plans come with a 30-day money-back guarantee that I personally tested to be trustworthy. I sent a message via 24/7 live chat and the agent asked for my payment details before approving my refund request. I had my money back 6 days later.
Surfshark works with: Netflix, Disney+, Max, Hulu, Amazon Prime Video, BBC iPlayer, Sling TV, and more.
Surfshark works on: Windows, macOS, Linux, Android, iOS, Chrome, PlayStation 4, smart TVs, routers, and more.
Easy Setup Guides: How to Install a VPN on Any Device
Most VPNs, including the ones I’ve listed above, are extremely easy to install and use — the whole process takes less than 5 minutes. Just sign up for a VPN service, install the app, and log in. The steps may vary depending on the VPN and operating system you’re using. If you’re having problems, you can check out the guides on your VPN provider’s website.
But first, try these step-by-step guides for desktops, mobile devices, routers, and smart TVs:
Windows and Mac
Many VPNs offer native apps for Windows, macOS, and even Linux. The installation process is similar across all operating systems:
- Subscribe to a VPN using the official website. Choose a service that meets your needs. I recommend ExpressVPN as it’s the best in 2024 for Windows and Mac devices.
![Screenshot of ExpressVPN's homepage Screenshot of ExpressVPN's homepage]()
- Download the VPN to your device. Get the software from the website and click the downloaded file from your browser to start installation.
![Screenshot of ExpressVPN's app download page Screenshot of ExpressVPN's app download page]()
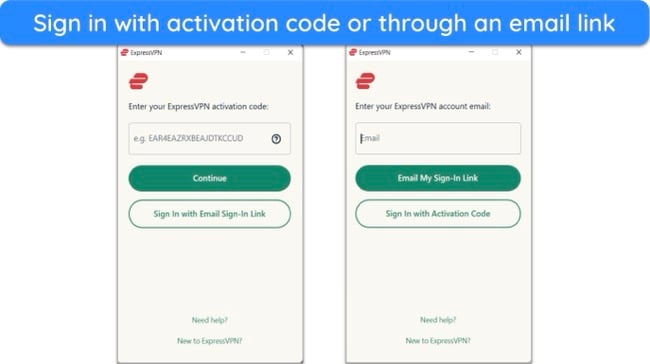
- Sign in with your VPN account details. This could be your username and password, or an authentication code provided by your VPN.
![Screenshot of ExpressVPN's app download page Screenshot of ExpressVPN's app download page]()
- Connect to a VPN server of your choice. You’re now ready to start using the internet securely.
![Screenshot of ExpressVPN's servers list Screenshot of ExpressVPN's servers list]()
Android, iOS, Tablets, and Amazon Fire Stick
To ensure you can access the money-back guarantee, get the VPN apps directly from its official website instead of relying on an app store and follow these steps:
- Download a VPN from the official website. Most VPNs have native apps for both Android and iOS devices.
- Open the VPN app and log in. You’ll need the account details you created on signup.
- Connect to a server. Tap on a server of your choice or let your VPN choose the best option.
- It’s done. Your smartphone is now protected by a VPN.
Smart TVs, Roku, and Streaming Devices
Roku, most smart TVs, and streaming devices don’t support VPN apps natively. If you have a smart TV running on Android OS, ExpressVPN has a native Android TV app that might save you the hassle of connecting through a router.
But if you can’t use a VPN app with your device, you have to first install the VPN on your router. Then, connect your device to your router and it will automatically connect to the remote VPN server. Although the steps vary from one platform to another, this is the general method:
- Check router compatibility. Note your router’s model and make, and visit your chosen VPN’s website to determine compatibility. If you have an Asus, Linksys, or Netgear router, ExpressVPN has its own firmware for easy installation.
- Install the VPN. You can find the specific installation guide for your router on the VPN’s website.
- Connect to a server. The VPN guide will also tell you how to connect to one of its servers on your router.
- Start streaming. Connect your streaming device to your router and you can watch your favorite shows.
You can also create a WiFi hotspot from your VPN-protected computer and connect your smart TV to the hotspot. This sharing connection will let your smart TV benefit from the VPN encryption — and you can easily disconnect your TV when you’re done.
A third option is to set up Smart DNS with your smart TV. This changes the DNS server your smart TV uses, so you can access your local streaming services. However, this doesn’t provide the encryption of a regular VPN connection. ExpressVPN has a MediaStreamer feature designed for smart TVs, with easy step-by-step setup instructions on its website.
Alternatives to VPNs
VPN Browser Extensions
VPN browser extensions hide your IP address so you can browse and stream anonymously. Some extensions, like CyberGhost’s Chrome and Firefox proxies, are free. You’ll usually have access to a few servers and they can connect to your favorite streaming services.
However, the majority of VPN browser extensions are proxies that don’t encrypt your connection, so they’re not ideal for sending sensitive data or preventing spying eyes from viewing your online activity. Plus, a browser extension only covers your browser traffic, not your entire device.
If you must use this option, ExpressVPN’s browser extension will give you the same military-grade encryption and data leak protection as the app. You can use it conveniently from your browser and connect to any of its 3,000+ servers, so you’re not limited to a handful of locations.
Tor Browser
Tor (The Onion Router) browser is free and works like a regular browser. But instead of sending your traffic directly to the destination, it’s routed through several different volunteer computers, or “nodes” that also encrypt your data. Each node can see where your data is coming from and going to, but not the entire route from your device to the destination site.
Tor provides almost complete anonymity, as it’s nearly impossible to trace your online activity back to you. This makes it useful for accessing the dark web or sending and receiving highly sensitive information.
However, the Tor browser has its limitations — it’s extremely slow, is easily blocked by ISPs and other networks, and it only secures your browser traffic, not your entire device. This makes it vulnerable to data leaks, and you’ll find Tor traffic also a target for surveillance.
The only way to mitigate these risks is by using a VPN with Tor. By connecting to a VPN server before the Tor browser, you secure your entire device (preventing data leaks) and you don’t expose your true IP address to Tor. This eliminates the risk of your location or identity being discovered through deanonymizing attacks by compromised nodes.
Proxy Services
A proxy service passes your traffic through a third-party server, hiding your IP address and location. This can provide access to restricted websites and allow you greater anonymity on the internet.
However, you won’t get any extra security with a proxy server. There is no encryption, no kill switch, and no data leak protection. Some proxies even tell your destination website that you’re using a proxy service, which increases the chance of your connection being blocked.
A VPN is a much better option if you value your online security and privacy, as it encrypts your entire internet connection and routes your traffic through secure servers. Nobody can see which websites you visit, what files you’re torrenting, or even the shows you’re streaming.
FAQs on VPNs
How does a VPN work for beginners?
A VPN works by encrypting your data within a secure tunnel before it reaches its online destination. High-level encryption stops your ISP, hackers, spies, and government bodies from seeing what you’re doing online. Your data can only be unencrypted by the VPN server you connect to, which then sends your traffic to the website or service you want to access.
When your traffic reaches its destination, the website or service can only see that the data has come from the VPN server — it can’t trace the traffic back to your device or your true location. This lets you access restricted content, visit websites and online accounts securely, bypass tough firewalls, and more.
What should I know before using a VPN?
There are a few things you should consider before using a VPN:
- Not all VPNs offer the same level of security and privacy. All VPNs claim to be the best, but only the top services will protect your online activity and keep your data safe.
- A VPN doesn’t make you completely anonymous. Your VPN connection provides a layer of anonymity, but your activity can still be traced if you log into your online accounts, make purchases and do other similar actions.
- A VPN doesn’t give you the right to break the law. You cannot use a VPN to commit illegal activities, like sharing copyrighted content, cyberbullying, hacking, and distributing malicious software.
- VPNs aren’t legal to use in every country. Make sure you’re aware of your local laws and regulations regarding VPN use before connecting, as some countries ban or heavily restrict VPN software.
Is it legal to use a VPN?
Mostly, but it depends on where you are. Using a VPN to protect your online privacy and security is legal in most countries and you are well within your rights to do so. Using a VPN is the best way to secure your data. But, there are a handful of locations that heavily restrict or outright ban the use of VPNs that aren’t approved by the government.
You’ll usually find that there are legal implications to using a VPN in countries where the internet is highly censored. China, Russia, and the UAE are a few examples.
I strongly recommend you check your local laws and regulations surrounding VPNs before connecting to a server, especially if the country you’re in censors a lot of online content. Otherwise, you could face repercussions. My team and I don’t condone participating in any illegal activity, so please be careful and inform yourself!
Does a VPN slow down your internet connection?
Yes, a VPN will slow down your internet connection slightly. The best VPNs won’t noticeably slow down your connection as they are designed to mitigate the speed loss caused by encryption. But you can expect some reduction in speed because your data has to travel via the VPN server, rather than directly to its destination.
However, different VPNs experience different speed reductions, so it’s important to make comparisons. Your internet speed will also vary depending on the server you choose. Distant server connections increase the amount of time it takes to send your data and receive a response. Connecting to a local server will result in a faster connection.
Can I be tracked while using a VPN?
Yes, you can be tracked while using a VPN. There are ways you can be tracked even if you’re connected to a VPN server:
- Logging in to your personal accounts — if you access your Netflix account, Gmail, or Facebook profile, the service will know it’s you. It will track your activity while you’re using it, even if you’re using a VPN.
- Data leaks — DNS requests, your IP address, and WebRTC data can all leak despite your VPN’s encrypted connection. Make sure you use a VPN with its own DNS servers and built-in data leak protection.
- Cookies and digital fingerprinting — these are methods for websites and advertisers to track your online habits, regardless of your VPN connection.
- Malware — malicious software like keyloggers, ransomware, and spyware can track your activities, login details, and more.
A VPN will keep your browsing activity private and safe from your ISP, hackers, or anyone else watching. However, it can’t provide total anonymity or stop you from being tracked entirely, despite assigning a new IP address.
The difference between privacy and anonymity is that privacy is like a shield, blocking prying eyes from seeing what you’re doing. Anonymity is like a mask — others can see your actions, but can’t see that it’s you performing them. A VPN provides layers of privacy and anonymity, but it can’t keep you completely unidentifiable online.
VPNs also can’t operate without seeing your online activity — otherwise, they can’t address DNS requests or troubleshoot connections. If you download a VPN with poor privacy practices, it’s possible to get caught even if you’re connected through Tor or using other advanced features. A good VPN service won’t keep logs or store identifiable data that can be traced back to you.
Can you trust a free VPN?
Not all of them. The only VPNs you can truly trust are premium services like those listed above. These VPNs have strong security and strict privacy policies, ensuring your online activity and personal data are safe while you’re connected. Plus, services like ExpressVPN are trustworthy — they haven’t been embroiled in scandals and won’t sell your data to third parties.
There are some safe and secure free VPNs that won’t log or store your data, but you’ll find they may be missing security features like a kill switch, split tunneling, or server obfuscation. They also have other limitations, like data caps, server restrictions, and speed throttling, which means you can’t use them as much as you want to.
Do VPNs protect against hackers and malware?
Yes, by disguising your true location and encrypting your data. A VPN can stop hackers from finding out who you are to protect you from identity theft, fraud, and even issues like DDoS attacks when gaming online.
Most VPNs don’t offer this service, but all the VPNs on this list have some form of protection against malware. However, a VPN isn’t an effective tool against viruses, spyware, ransomware, and others. It’s better to get an antivirus service to use with your VPN, as this is a more comprehensive solution.
Which devices do VPNs work on?
What’s the best VPN for Netflix?
The best VPN for Netflix is ExpressVPN. Its fast speeds, global server network, and top-tier encryption mean ExpressVPN consistently works with Netflix so you can watch your local library.
Streaming services like Netflix block VPN IP addresses aggressively to protect their licensing agreements, so most VPNs don’t work. Fortunately, ExpressVPN refreshes its IP addresses regularly to make sure they always work reliably with Netflix.
It’s important to note that you shouldn’t use a VPN to access Netflix content from libraries outside of your location. This could constitute copyright infringement and it goes against Netflix’s Terms of Service. My team and I don’t condone this behavior.
How do I know my VPN is working?
Do VPNs keep logs?
Should a VPN be left on at all times?
You can leave your VPN on at all times, but you don’t have to. The best VPNs have unlimited data and won’t slow your internet speeds, so you don’t have to worry about switching them off — you won’t even notice it’s on. Plus, your VPN should have a kill switch to cut access to the internet, protecting your data if the VPN connection is interrupted.
If you’re concerned about your online privacy or live in a country with tough internet restrictions, it makes sense to leave your VPN connected at all times. I’d also recommend keeping your VPN on or using a VPN with an auto-connect feature with your mobile devices — this will ensure your data security when you switch between networks, especially if you connect to public WiFi.
What’s the most secure VPN protocol?
Overall, the most secure protocol is OpenVPN. All the best VPNs support OpenVPN, which is known for its security, speed, and reliability. Many VPNs now also support the WireGuard protocol, which is designed for speed and security and is much more lightweight than OpenVPN — just 4,000 lines of code compared to OpenVPN’s 600,000.
Others include ExpressVPN’s proprietary Lightway protocol and IKEv2 (good for mobile devices). The security of your VPN depends on more than just its protocols, though. You should choose a trusted provider with proven security features. Also, note the provider’s company headquarters and privacy policy to ensure your online activity and personal data are secure.
In Summary – What is a VPN and Why Do You Need One?
A VPN is security software designed to protect your data and internet activities as online threats increase. New technologies continue to develop and hackers are becoming more sophisticated in stealing data and committing cyber crimes. By connecting to a VPN server before going online, you keep your personal information to yourself and claim back your right to privacy.
If you haven’t started using a VPN, they’re not difficult to use — most VPNs are easy to set up on all major devices. Of all the services tested, ExpressVPN is the best VPN for beginners due to its easy-to-use apps, fast speeds, and impressive network size. It also comes with a 30-day money-back guarantee, so you can try it for the first time without any risks.
Glossary of Common VPN Terms
| VPN Term | Description |
| 5/9/14 Eyes Alliance | International security alliances work together to collect and share internet surveillance data. Some countries include the US, Canada, UK, etc. |
| Encryption | Scrambling data with a code for secure transmission. |
| IP Leaks | When your VPN fails to hide your true IP address. |
| ISP | Stands for Internet Service Provider. The company you pay for internet access. |
| Kill Switch | Automatically cuts off your internet if the VPN connection isn’t secure, preventing data leaks. |
| Logs | Data your VPN provider stores about your online activity. |
| Multi-Hop | Routes your internet connection through 2 VPN servers for enhanced privacy. |
| Proxy Server | Acts as an intermediary between your device and the internet, hiding your IP address. |
| Router | Device that sends data between networks. Provided by your ISP for internet access. |
| TOR | Software for anonymous online communication. Routes data through a volunteer network, making it difficult to track the source. |
| VPN Client | Program installed on your device to connect to a VPN server. |
| VPN Protocol | Set of rules for secure communication between VPN clients and servers. Some protocols offer better security than others. |
| VPN Server | Computer managed by your VPN provider that you connect to using your VPN client. Your data is routed through this server, masking your location and IP. |
| VPN Service | Increases security by encrypting your internet traffic and hiding your IP address. Also allows bypassing censorship by appearing in a different location. |