What Is a No-Log VPN & Why VPN Log Policies Matter 2026
A VPN’s purpose is not just to change your IP address and unblock streaming sites. A reliable VPN protects your online privacy too. Like internet providers, some VPNs store logs about your online activity, which the authorities, advertisers, and even hackers can access and exploit.
Only a no-log VPN can keep your data private and guarantee your anonymity online. No-log VPNs are also the best VPNs for torrenting as they keep ISPs from tracking your activities and throttling your speeds.
The problem is that almost all VPNs claim not to keep logs, so I tested over 30 VPNs and their privacy policies to see which ones truly keep no logs and if there is such a thing as a no-log VPN. After testing, I found ExpressVPN is the best no-log VPN, with a proven record of keeping zero information on users. Editor’s Note: Transparency is one of our core values at WizCase, so you should know we are in the same ownership group as ExpressVPN. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
Get ExpressVPN for anonymous browsing
Note: VPN logging policies are subject to change. While we’ll endeavor to keep this article updated, we advise that you always cross-check the information here with what’s stated on each provider’s website.
Types of VPN Logs: Which Ones Threaten Your Online Security?
Logs are records of information transmitted across networks, created whenever you visit a website through your ISP. This log will usually detail your IP address, the site you visited, time of connection, what you did, and how long you spent on the site.
Third parties can use some of this data to identify you, determine your location, and track your browsing habits. For instance, your ISP can tell if you’ve connected to Netflix from New York and streamed/downloaded shows for 2 hours. This information is seemingly harmless, but marketers can exploit it to send you targeted ads, or it can be used to track your torrent activity. Law enforcement agencies could even use this information to trace a suspect.
When you use a VPN, you’re swapping out your ISP’s logs for the VPN since it routes your internet traffic through its encrypted tunnel. VPN logs are the data that VPN providers store regarding the usage of their service. Since VPNs promise to keep you anonymous, the VPN you choose needs to have a solid no-log policy.
A no-log policy shows that a VPN won’t store any record of your online activity. Sometimes, this only covers logs that can be traced to you. VPN providers may still store other types of data.
There are 3 types of VPN logs:
- Connection Logs
- Usage Logs
- User Information
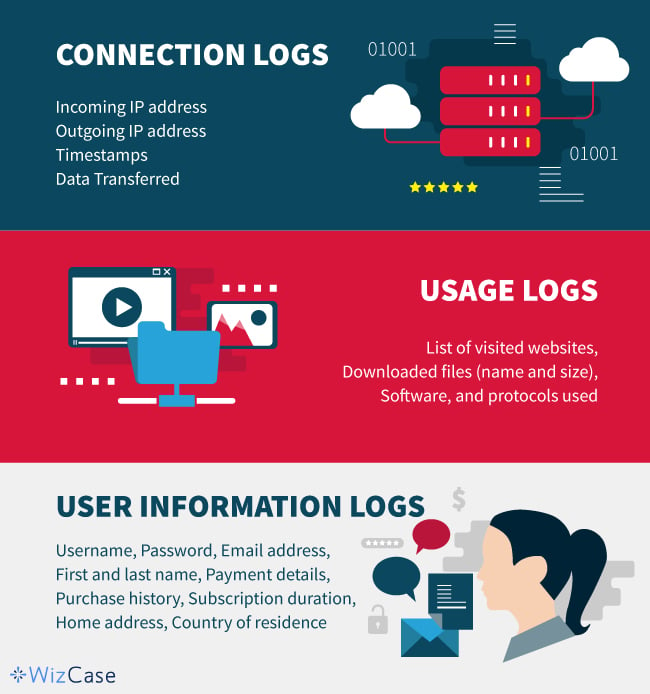
Connection Logs
Connection logs record all incoming and outgoing connections to a VPN server. VPNs typically use this data to maintain the quality of their service and troubleshoot issues. These logs may consist of:
- Incoming IP address: The address your ISP assigned to your device.
- Outgoing IP address: The address assigned to you when you select a VPN server.
- Timestamp: Time your VPN connection starts and ends.
- Data Transferred: The amount of data uploaded and downloaded in a session.
VPNs need to store some connection logs to efficiently run their service, such as providing support and monitoring data caps. For example, if your VPN sets device limits then it’s keeping some connection logs.
It’s hardly an issue if a VPN stores the bare minimum — some connection logs can’t be traced to one user. However, trackers can use IP address logs to connect your activity to you. Generally speaking, you should avoid VPNs that store IP connection logs.
That’s why privacy-conscious VPNs don’t store this data. For example, ExpressVPN doesn’t store connection logs. The little it keeps is anonymized, so, even if hackers gain access to ExpressVPN’s servers, they can’t connect your VPN activity to you.
Usage Logs
VPN providers have access to the same information as your ISP once you connect to a server and your internet traffic is routed through the VPN tunnel. Some governments require ISPs to store records of their user’s online activity. If VPN providers were to log the same information, this is what they may store:
- List of websites you visit
- Downloaded files (name and size)
- Software and protocols you used (such as Netflix, BitTorrent, Skype, etc.)
Usage logs are also known as activity logs, and they are very invasive. Whoever gains access to this data can discover your browsing habits and the actions you take while you’re online. Unfortunately, free VPNs like Hola VPN store your usage logs and may sell them to third parties for advertising. This defeats the whole point of using a VPN for increased online security, privacy, and unrestricted internet access.
No reputable VPN provider will routinely keep usage logs (at least not one we’d ever recommend). In fact, premium VPN providers like Private Internet Access offer advanced security features and infrastructure like RAM-based servers that make it practically impossible for them to store logs.
User Information
VPNs may also store user data that helps them conduct business operations and prevent fraud. It typically includes some or all of the information below:
- Username
- Password
- Email address
- First and last name
- Payment details
- Purchase history
- Deal duration
- Home address
- Country of residence
User information logs are mostly harmless records that are necessary for conducting business. However, VPNs that store identifiable connection logs and personal information put your security at risk. If hackers ever compromise the VPN’s servers, you could be the victim of malware attacks or identity theft.
Oppressive governments could also use personal information and connection logs to track dissidents. This is why it’s best for a VPN to have little information on you and your activities as possible. The best no-log VPNs let users register with temporary email addresses and offer multiple anonymous payment options..
Top Tip: Your IP address is usually associated with your payment details. For added safety, sign up for a VPN with a disposable email account, then pay anonymously using cryptocurrency.
Why You Should Care About a VPN’s No-Log Policy
The data collected from your VPN usage could let people know quite a bit about you. Even if you don’t visit questionable sites and think you have nothing to hide, VPNs can sell your data to third parties for marketing purposes. It is a breach of trust when a platform that claims to secure your information sells it instead.
There are some logs that a VPN should not keep under any circumstances:
- The messages you send and receive.
- The websites you visit.
- The services you use.
- Your original IP address.
However, some conditions may compromise a VPN’s logging policy. For example, the VPN’s country of incorporation. Data retention laws vary, and some countries require VPNs to keep logs for a certain period should law enforcement officials need access to them. Data surveillance alliances like the 5, 9, and 14 Eyes are one reason why some states are more privacy-friendly than others. Countries like the US and UK jointly agree to monitor and share their citizens’ online data with other states.
Unfortunately, some VPNs claim to be no-log services and still keep usage or connection logs. For example, popular VPNs like Windscribe, Betternet, and ThunderVPN say they don’t keep records yet store connection logs.
Keep in mind that VPN log policies are hard to prove or disprove. So, when choosing a VPN provider, it’s always best to read reviews. Look for services with detailed privacy policies. Researching the provider’s history is also a good idea since some VPNs have had cases where the authorities requested data. If a service did hand over user information, you’ll know its no-log policy could be a hoax.
Stay safe online with ExpressVPN
Editor’s Note: Transparency is one of our core values at WizCase, so you should know we are in the same ownership group as ExpressVPN. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
Quick Guide: Best No-Log VPNs in 2026
- ExpressVPN — #1 proven and audited no-log VPN with advanced security features and RAM-based servers. Try ExpressVPN risk-free!
- CyberGhost — Based in privacy-friendly Romania with regular transparency reports but no independent security audit.
- Private Internet Access (PIA) — Proven no-logs policy, but it is headquartered in the US.
- NordVPN — Located in Panama where intelligence sharing laws don’t apply, but it might share data with governments if legally required.
- Surfshark — A no-log claim that’s verified by a Big Four audit firm, but it’s within the jurisdiction of the 9 Eyes Alliance.
- PrivateVPN — Solid no-logs policy and DNS protection, but no third-party audit, and it’s located in Sweden, which is a member of the 14 Eyes alliance.
- IPVanish — Zero-logs policy, but it has had some logging scandals and doesn’t accept cryptocurrency payments.
Browse anonymously with ExpressVPN
Editor’s Note: We value our relationship with our readers, and we strive to earn your trust through transparency and integrity. We are in the same ownership group as some of the industry-leading products reviewed on this site: ExpressVPN, CyberGhost, Private Internet Access, and Intego. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
The Best No-Log VPNs for Anonymous Internet Access (Tested in 2026)
1. ExpressVPN — Verified No-Logs Policy with RAM-Based Servers for Zero Data Retention
Key Features:
- 3,000 obfuscated servers in 105 countries to keep you anonymous online
- Independently audited and proven no-log policy
- TrustedServer technology uses RAM-only servers for added security
- Advanced IPv6, WebRTC, and DNS leak protection with ExpressVPN’s private DNS on every server
- Protects up to 14 devices simultaneously
- 24/7 live chat, email support, and online guides
- 30*-day money-back guarantee to try out ExpressVPN risk-free
ExpressVPN is one of the most secure no-log VPNs with an audited and verified log policy. PricewaterhouseCoopers (PwC) tested and endorsed its security infrastructure and no-log policy. An incident involving the Turkish government further proved ExpressVPN’s no-log claims better than any audit. Back in 2017, Turkish authorities seized one of its servers in hopes of gaining information on a potential criminal case.
While ExpressVPN had to cooperate with the government, the authorities could not retrieve identifiable user data from the server. In 2022, ExpressVPN underwent two additional audits by KPMG and Cure53, and both verified that ExpressVPN still upholds its exceptional standards.
During my tests, I found that all ExpressVPN servers run on a RAM-only system. It calls this the TrustedServer technology. Unlike traditional hard disk drives that retain data and are more susceptible to security breaches, ExpressVPN’s RAM servers wipe all data after every reboot. Even if an ExpressVPN server is compromised, no traceable data can be found since nothing is being stored on disks.
Another security advantage is that ExpressVPN headquarters is in the British Virgin Islands where there are no data retention and reporting laws. The BVI is also outside the jurisdiction of the 5/9/14 Eyes alliances that are notorious, for data surveillance. Located here makes it easy for the VPN provider to put user privacy at the forefront and uphold its log policy.
Having come across several vague and sketchy privacy statements, I appreciate ExpressVPN’s extremely detailed privacy policy. It clearly states that ExpressVPN doesn’t store logs of your browsing history, message content, IP address, and DNS queries.
ExpressVPN only keeps information about your apps and their versions and the days you use the VPN (not specific times). It also knows the location you connect to (but not the assigned IP address) and the amount of data transferred in a session. These logs are anonymized, accessed only to resolve issues, and can’t be used to trace any activity back to you.
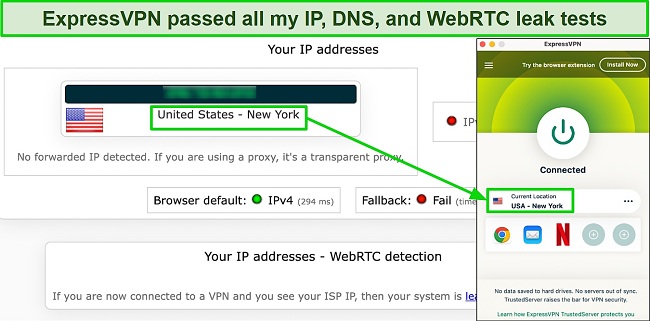
I wanted to see how well ExpressVPN secures your data, so I ran multiple leak tests. I connected to 18 server locations in 6 countries, and none of them exposed my IP address or DNS requests. You also get the following features:
- A kill switch that instantly cut web traffic when I tested it by stopping the VPN as I loaded a page. This means your real IP is never revealed
- AES 256-bit encryption which is almost impossible to breach
- TOR compatibility, so you can download ExpressVPN from its own .onion website for extra anonymity.
This VPN also delivers superfast speeds and the most reliable connections of the VPNs I tested. When I tried its servers in the US, UK, and Germany, I averaged 100 Mbps. That’s enough to watch Netflix US in 4K and torrent large public-domain files via BitTorrent. ExpressVPN has over 3,000 servers worldwide, so there’ll always be an option close to you.

You can pay for ExpressVPN with cryptocurrency, which I recommend if you’re big on privacy. The only downside is that ExpressVPN is a bit pricier than other premium VPNs on this list. But I believe its advanced security features and fast speeds make it a bargain.
Try out ExpressVPN risk-free. It’s backed by a 30*-day money-back guarantee, so you can ask for a refund if you’re not satisfied. I tested this myself by using ExpressVPN for 2 weeks before requesting to cancel my account via live chat. I didn’t have to answer several questions or deal with much back and forth, so the refund approval was fast. I had my money back 5 days later.
Editor’s Note: Transparency is one of our core values at WizCase, so you should know we are in the same ownership group as ExpressVPN. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
ExpressVPN works with: Windows, macOS, Linux, Chromebook, Android, iOS, Chrome, Firefox, Edge, PlayStation, Xbox, Nintendo Switch, Amazon Fire TV, Amazon Fire TV Stick, Nvidia Shield, Xiaomi Mi Box, Google Chromecast, Roku, Android TVs, smart TVs, routers, and more.
ExpressVPN also unblocks: Netflix, Disney+, Hulu, HBO Max, Amazon Prime Video, Paramount+, Peacock, Discovery+, Showtime, BBC iPlayer, BritBox, Starz, Crunchyroll, fuboTV, Sling TV, DirecTV, YouTube TV, Kodi, and more.
Stay anonymous with ExpressVPN
2026 Update! You can subscribe to ExpressVPN for as low as per month with a 2-year + 4 months purchase (save up to %)!! This is a limited offer so grab it now before it's gone. See more information on this offer here.
2. CyberGhost — Strict No-Logs VPN Located in Privacy-Friendly Romania With Quarterly Transparency Reports
Key Features:
- 11,690 servers in 100 countries to connect with privacy from anywhere
- No-logs policy and audited security features to stay private online
- Headquartered in privacy-friendly Romania so nobody can access your data
- CyberGhost-owned NoSpy servers add an extra layer of privacy
- Secure all your devices with up to 7 simultaneous connections
- Live chat support in English, French, German, & Romanian and email support
- 45-day money-back guarantee to test out CyberGhost
CyberGhost is a zero-logs VPN based in Romania — a country known for its pro-privacy laws. The Romanian government rejected the EU’s data retention laws, so companies under its jurisdiction aren’t required to store user data. Romania is not a member of the 5/9/14 Eyes alliance, allowing CyberGhost to adhere to a strict no-log policy. I researched CyberGhost’s no-log policy and found that it does not monitor, record, log, or store your browsing history, search habits, transferred data, or IP address.
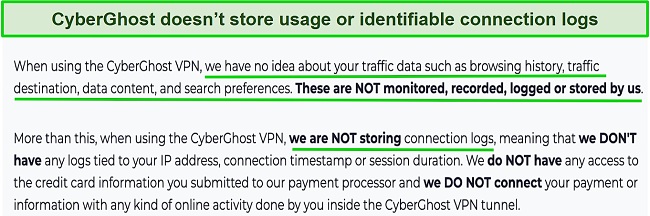
To prove its commitment to user privacy, CyberGhost was the first VPN to start publishing yearly transparency reports. It now issues these reports every three months. Transparency reports show the number of legal data requests CyberGhost receives from the police, lawyers, and websites. These reports give me confidence in the VPN’s service because it never discloses any data.
CyberGhost’s no-log policy has undergone a third-party audit that verified the efficacy of its no-log policy. Additionally, the VPN did pass its Information Safety Management System audit and has never had a known case of storing user information.
I found that CyberGhost owns some of its servers for added security. These “NoSpy” servers are managed in-house in the company’s private data center. This means CyberGhost personnel can easily control access to them. The NoSpy servers also use high-grade hardware, so you get better performance than regular servers. That doesn’t mean the other servers aren’t good. CyberGhost has optimized servers in 100 countries for torrenting and streaming that deliver fast download speeds and HD streams.
It has built-in leak protection to keep your identity safe while browsing. To confirm this, I connected to multiple servers and ran IP and DNS leak tests. My test proved that CyberGhost would not leak your IP address or DNS queries, as it only detected requests from the VPN server I was using. An automatic kill switch stops all internet traffic if your VPN connection gets unsteady.
In addition to using military-grade encryption and current VPN protocols like WireGuard, CyberGhost also has a built-in malware and ad blocker. The only issue is that it doesn’t always block ads. After noticing banners and video ads on sites like BuzzFeed, I contacted CyberGhost support and the agent told me the service only blocks ads that contain malware. I’d have preferred zero ads, but it’s good to know I’ll only see harmless adverts when using the VPN.
If you’d like to test it first, this VPN has the most generous money-back guarantee on this list. You can test out CyberGhost’s secure servers and no-logs features risk-free for 45 days. After testing CyberGhost for a few weeks, I requested a refund over the live chat and had my money back in my account in 5 days.
Editor’s Note: Transparency is one of our core values at WizCase, so you should know we are in the same ownership group as CyberGhost VPN. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
CyberGhost works with: Windows, macOS, Linux, Android, iOS, Raspberry Pi, Chrome, Firefox, PlayStation, Xbox, Nintendo Switch, Amazon Fire TV, Amazon Fire TV Stick, Roku, smart TVs, routers, and more.
CyberGhost also unblocks: Netflix, Disney+, Hulu, HBO Max, Amazon Prime Video, Paramount+, Peacock, Discovery+, BBC iPlayer, Canal+, Globo, Crunchyroll, Yle, Foxtel, fuboTV, YouTube TV, Kodi, and more.
Stay anonymous with CyberGhost
2026 Update! You can subscribe to CyberGhost for as low as per month with a 2-year purchase (save up to %)!! This is a limited offer so grab it now before it's gone. See more information on this offer here.
3. Private Internet Access — A Proven Zero Logs Policy And Multiple Advanced Security Features
Key Features:
- Over 29,650 servers in 90 countries keep you anonymous from anywhere
- No-log policy has been proven in real-life cases
- Blocks ads, malware, and trackers with MACE
- Shadowsocks and SOCKS5 proxies to bypass firewalls
- Protect up to unlimited devices at the same time
- Extensive knowledge base, 24/7 live chat, and email support
- 30-day money-back guarantee to try PIA without commitment
Private Internet Access (PIA) has a strict no-logs policy and records to back it up. The Russian government once seized PIA’s physical servers but couldn’t find any user data. There was also a court order where the FBI requested information on a PIA customer. But, again, the VPN couldn’t provide any because it doesn’t keep logs. Real-life events like these are ways a VPN service can prove its no-log claims, and PIA is one of the few no-log VPNs that is proven to live up to its promises.
During my tests, I discovered that PIA offers highly customizable VPN settings, so you’ll have more control over your security options. For example, you can choose between AES 128-bit and 256-bit encryption (they’re both very secure) and set automated connection rules for specific WiFi networks. There are also 2 VPN protocols available, OpenVPN and WireGuard, and you can decide to activate PIA’s multi-hop feature. Multi-hop adds an extra layer of security since it routes your VPN traffic through two locations.
I like that PIA switched to RAM-based servers — they are more secure than regular disk servers. A simple reboot is all it takes to wipe data off a RAM server. PIA’s NextGen VPN servers also offer more robust security and faster speeds thanks to improved hardware and 10Gbps network cards.
Its servers support P2P traffic, and offer port-forwarding, which can give you faster download speeds while torrenting. You can easily activate port forwarding from the Network tab under Settings. To ensure PIA keeps you safe while torrenting, I tested for IP and DNS leaks, but it never exposed my actual IP address. The kill switch also blocked my network whenever I switched VPN servers or my internet was down.
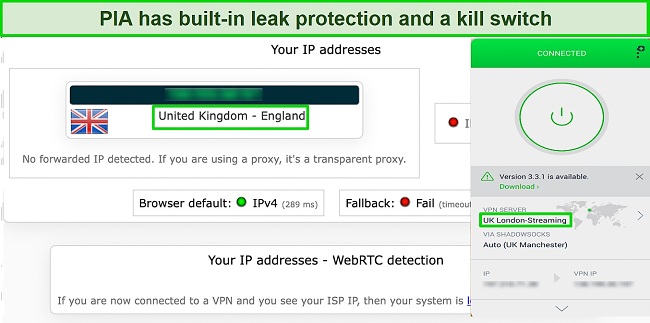
A minor con is that PIA is located in the US, the center of the international surveillance alliance. The VPN has been audited by a third-party firm called Deloitte, which found PIA’s policies to be as air-tight as it claims.
Editor’s Note: Transparency is one of our core values at WizCase, so you should know we are in the same ownership group as Private Internet Access. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
PIA works with: Windows, macOS, Linux, Android, iOS, Chrome, Firefox, Opera, Amazon Fire TV, Amazon Fire TV Stick, routers, and more.
PIA also unblocks: Netflix, Disney+, Hulu, HBO Max, Amazon Prime Video, Showtime, Discovery+, Canal+, Crunchyroll, Yle, Vudu, UKTV, 9Now, CBC, YouTube TV, and more.
2026 Update! /month for a two-year plan with 2 months free (%)!! This is a limited offer so grab it now before it's gone. See more information on this offer here.
4. NordVPN — Premium VPN With Cheap Prices on Long-Term Offers
Key Features:
- Short and long-term offers available
- 30-day money-back guarantee
- 9,419+ global servers in 137 countries
- Unlimited bandwidth
- Protect up to 10 devices at once
NordVPN is one of the best VPNs on the market — and you can get super cheap prices when you sign up for a long-term offer. One thing to note, however, is that when it’s time to renew your offer, prices do increase quite significantly.
I was particularly impressed with the high performance of every server I tested. Just because a VPN has thousands of servers doesn’t mean they all work. Servers can still struggle to work — and some can even fail to connect completely. However, NordVPN’s servers work with Netflix for smooth, buffer-free streaming.
I did, however, have issues with using NordVPN’s native Fire TV app. Although it mostly worked with Netflix, it sometimes had issues and kept crashing. I also found that NordVPN’s user interface for desktop devices was less user-friendly than ExpressVPN and CyberGhost.
NordVPN has the following security and privacy features:
- AES 256-bit encryption
- kill switch that cuts your internet access if your connection to a VPN server drops suddenly
- built-in ad and malware blocker, so you don’t need a third-party ad blocker
- fully audited no-logs policy (audited by PwC) – NordVPN doesn’t store any personal or identifying data while you’re connected to the VPN
In addition, NordVPN includes Threat Protection that protects you from viruses, infected websites, and trackers – and it works whenever you have the NordVPN app open, even if you’re not connected to a VPN server.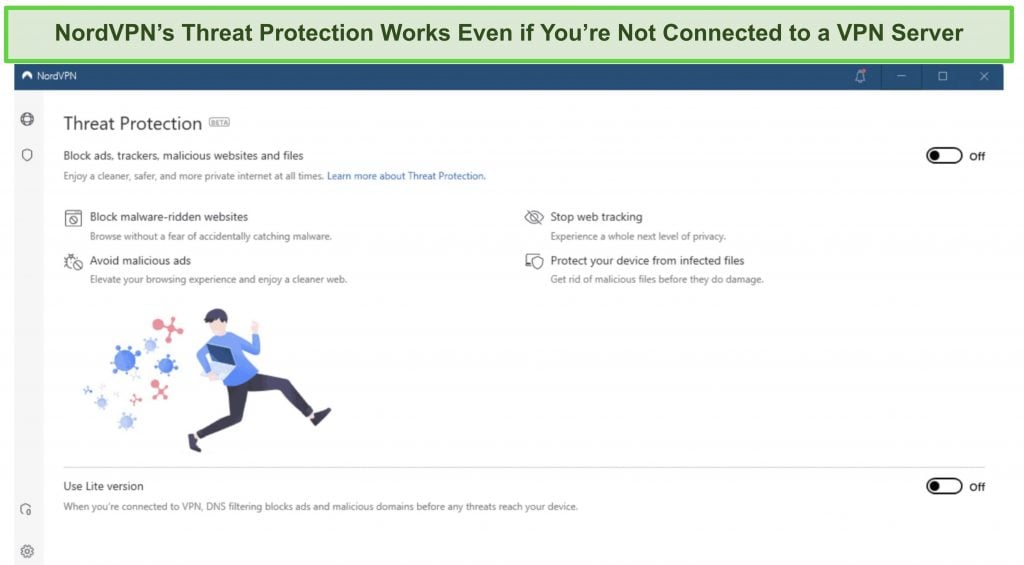
It's easy to find a NordVPN offers that suits your needs. You can also stream, torrent, and browse for free for up to 30 days with its money-back guarantee. I tested this to ensure that you’ll really get your money back. At first, the support team tried to give me an extended trial period — but they initiated my refund right away after I told them I wasn’t interested in the extension. I got my money back in 6 business days.
NordVPN works with: Netflix, Amazon Prime Video, BBC iPlayer, Hulu, Disney+, SkyTV, HBO Max, SHOWTIME, DAZN, ESPN, YouTube TV, and more
NordVPN works on: Windows, Mac OS, Android, iOS, Windows Phone, Chromebook, Linux, Chrome, Firefox, Fire Stick, and Android TV
5. Surfshark — Best Value for Money with Unlimited Device Connections and Fast Speeds
Key Features:
- Short and long-term offers available
- 30-day money-back guarantee
- 4,500+ global servers in 100 countries
- No bandwidth restrictions
- Connect unlimited devices at once
Surfshark offers the best value for money out of every premium VPN on the market. You can connect an unlimited number of devices, which means you can use Surfshark on all your devices without getting logged out.
I tested Surfshark’s simultaneous connections on 2 PCs, 2 phones, a Fire Stick 4K, and an iPad. My connection remained reliable on all 6 devices. Even while I was actively streaming on all my devices, my average speed was 112 Mbps — fast enough for UHD quality.
When I saw the price of this service, I thought it couldn’t possibly have top-grade security features for such a low price, but I was pleasantly surprised.
Surfshark has the following security and privacy features:
- AES 256-bit encryption on all devices, with ChaCha encryption available for Android users
- Wireguard VPN protocol enabled by default
- diskless, RAM-only servers to protect your privacy (no data can be physically extracted from any servers)
- kill switch (although this isn’t enabled by default)
- IP and DNS leak protection
Surfshark offers two-factor authentication (2FA) on your account. This feature requires you to enter an extra code before you can log in to ensure that only you can access your account.
While Surfshark does have slightly fewer global servers than rivals such as CyberGhost and PIA, I didn’t experience any issues during my tests. I easily connected fast working servers every time, and I had excellent speeds for streaming, downloading torrents, and browsing the internet.
You can try Surfshark for yourself with the 30-day money-back guarantee. Requesting a refund is easy with Surfshark’s live chat feature. Although the support team asked why I wanted to cancel my offer, I had no problem getting my money back (and it only took 4 days!).
Surfshark works with: Netflix, Amazon Prime Video, Disney+, BBC iPlayer, Sling TV, HBO Max, DAZN, and more
Surfshark works on: Windows, Mac OS, Android, iOS, Linux, Fire Stick, Samsung Smart TVs, LG Smart TVs, Android TV, Kodi, and selected routers
6. PrivateVPN — Beginner-Friendly VPN That Doesn’t Keep Connection Logs
Key Features:
- 200 HQN servers in 63 countries to stay safe online
- No-logs policy (not audited) so none of your data is stored
- Large selection of VPN protocols, including OpenVPN and L2TP/IPSec
- Perfect Forward Secrecy encryption feature provides added security
- Supports up to 10 devices connections
- Customer support via 24/7 live chat and email support, with remote setup service available
- 30-day money-back guarantee
PrivateVPN is an easy-to-use no-logs VPN for beginners. Its simple UI (user interface) is easy to navigate, and you can quickly connect to a server once you launch the app. It also has apps for all the popular operating systems to protect all your devices. I found PrivateVPN’s extensive installation guides very helpful for setting it up.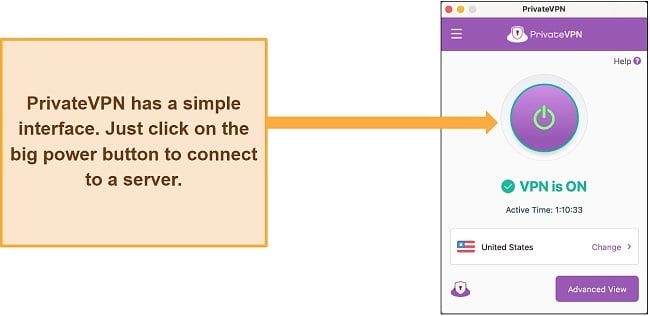
As an extra layer of security, PrivateVPN supports perfect forward secrecy, which changes your encryption key after every session. So, a hacker can’t gain access to your data even if they crack a past or future key. This VPN also offers:
- A kill switch that you can use with specific apps or system-wide, depending on your preferences
- Full IPv6 and DNS leak protection to stop your real IP from being seen
- Stealth Mode, which allows you to bypass network restrictions and guarantees more secure connections
It has an impressive selection of VPN security protocols. Depending on which one works best on your device, you can choose from OpenVPN TCP/UDP, L2TP/IPsec, and IKEv2. IKEv2, for example, is popular on Android and iOS mobile devices, and OpenVPN offers security and more reliable connections. Like the best VPNs I’ve tested, PrivateVPN protects your network with AES 256-bit cipher, an almost uncrackable encryption system.
I was disappointed to learn that PrivateVPN hasn’t had a third-party audit yet. Plus, having its headquarters in Sweden, which is part of the 14 Eyes alliance, gave me pause But, in its privacy policy, PrivateVPN states that it logs only the barest amount of data (email addresses and payment info) it needs to run its service efficiently. Your IP address, browsing habits, DNS queries, and connection logs are neither monitored nor stored.
You can also test PrivateVPN yourself for 30 days risk-free with its money-back guarantee. If you’re not satisfied with the service, contact customer support anytime within the 30-day guarantee period to get a full refund. I emailed support on the final day of the guarantee and had an email back later that day confirming the cancellation request. My money was returned 4 days later.
PrivateVPN works with: Windows, macOS, Linux, Chromebook, Android, iOS, Blackberry, Raspberry Pi, Chrome, Firefox, Amazon Fire TV, Amazon Fire TV Stick, Xiaomi Mi Box, Google Chromecast, Android TVs, routers, and more.
PrivateVPN also unblocks: Netflix, Disney+, Hulu, HBO Max, Amazon Prime Video, Paramount+, Peacock, Discovery+, BBC iPlayer, ITV Hub, RTE, fuboTV, YouTube TV, and more.
Stay anonymous with PrivateVPN
7. IPVanish — Fast No-Logs VPN That Owns All Its Servers For Added Security
Key Features:
- 3,200 servers in 112 countries to stay safe in any location
- Audited no-logs policy so your data isn’t logged or kept
- AES 256-bit encryption with DNS and IP leak protection
- IPVanish owns all its servers, eradicating third-party interference
- unlimited connections to protect all your devices
- 24/7 live chat, email support, and phone support in 6 countries
- 30-day money-back guarantee to try IPVanish without commitment
IPVanish owns all its 3,200 servers, so you don’t have to worry about a third-party data center not meeting the VPN’s standards. Many premium VPNs rent servers, so it’s impressive to see IPVanish go to these lengths to secure users’ privacy. Since it manages all servers, the VPN can address downtimes and any server-related issues as they occur.
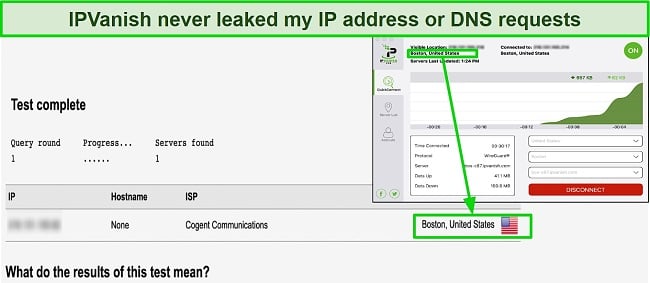
I found that IPVanish has a zero logs policy, certified in a third-party audit by Leviathan Security Group. This is a much-needed transparency move by the provider since a 2016 privacy incident revealed it had stored user data in the past. US authorities ordered IPVanish to turn over information on a suspect in a high-profile case, and the VPN complied, proving it stored logs. A different company has since acquired IPVanish, and its external audit proves it’s committed to keeping your data secure.
Regarding security, IPVanish is packed with great safety features, including:
- AES 256-bit encryption to make your data unreadable in the event a hacker accesses it
- Scramble setting helps you bypass geoblocked content by masking the fact that you’re using a VPN connection.
- IP leak protection, which you can manually turn off or on (I recommend keeping it on at all times)
Although it can’t match the speeds of ExpressVPN, IPVanish was one of the fastest VPNs of the 30+ I tested. Its WireGuard tunneling protocol consistently achieved high speeds even when I connected to distant servers. All its servers support P2P traffic, making IPVanish a good choice for torrenting.
But you don’t have to commit just yet — first try out IPVanish risk-free, with its 30-day money-back guarantee. If you’re not satisfied with the service, the cancellation process is simple. Just log in to your account and press the cancel deal button to process a refund. When I canceled my offer, I got my money back in just 3 days.
IPVanish works with: Windows, macOS, Linux, Chromebook, Android, iOS, Raspberry Pi, Chrome, Xbox, Firefox, Amazon Fire TV, Amazon Fire TV Stick, Roku, Google Chromecast, Android TVs, routers, and more.
IPVanish also unblocks: Netflix, Showtime, Discovery+, Paramount+, ITV Hub, ESPN, Vudu, and more.
Comparison Table: 2026’s Best No-Log VPNs
The premium VPNs I’ve mentioned here have strict no-logs policies and will protect your online privacy. However, some have better privacy features than others, such as being located in a privacy-friendly country. The following table compares the key no-log features of the VPNs on this list.
| Independently audited? | Located in a privacy-friendly country? | Stores browsing activity? | Stores your IP address? | Stores VPN IP address? | Stores bandwidth usage? | Stores connection time? | Accepts Crypto payments? | |
| ExpressVPN | ✓ | ✓ | ✘ | ✘ | ✘ | Aggregated | ✘ | ✓ |
| CyberGhost | ✓ | ✓ | ✘ | ✘ | ✘ | Aggregated | Aggregated | ✓ |
| PIA | ✓ | ✘ | ✘ | ✘ | ✘ | Aggregated | Aggregated | ✓ |
| NordVPN | ✓ | ✓ | ✘ | ✘ | ✘ | ✘ | ✘ | ✓ |
| Surfshark | ✓ | ✘ | ✘ | ✘ | ✘ | ✘ | ✘ | ✓ |
| PrivateVPN | ✘ | ✓ | ✘ | ✘ | ✘ | ✘ | ✘ | ✓ |
| IPVanish | ✓ | ✘ | ✘ | ✘ | ✘ | Aggregated | Aggregated | ✘ |
Protect your privacy with ExpressVPN
Editor’s Note: Transparency is one of our core values at WizCase, so you should know we are in the same ownership group as ExpressVPN. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.
What to Look Out for When Choosing the Best No-Log VPN
I tested over 30 providers and ranked them based on the criteria below to find the best no-log VPNs. You should keep these key indicators in mind when conducting your research:
- Strict and verified no-logs policy to prove a VPN is trustworthy and show they don’t store logs through actual court records. ExpressVPN, CyberGhost, and Private Internet Access have proven their policies in real-life cases.
- Independent third-party audits demonstrate a VPN’s confidence in its security infrastructure and policies. And if vulnerabilities are found during an audit, they can be fixed, consequently strengthening the VPN’s privacy features.
- Located in a privacy-friendly country that doesn’t have data retention laws and is preferably outside the jurisdiction of the 5/9/14 Eyes alliance. VPN providers headquartered in countries like the US, UK, Canada, Australia, and New Zealand may be subject to government regulations that require them to store user data.
- RAM-based servers make it harder to store logs since they erase all data once a session ends.
- Premium security features such as AES 256-bit encryption, IP/DNS leak protection, and a kill switch protect your data from malicious third-parties.
- Anonymous payment options like cryptocurrency add an extra layer of privacy to keep you from being linked to your use of the VPN.
- Fast speeds and reliable connections are important to stay safe online without dealing with laggy connections. The best VPNs combine advanced security features with high speeds.
- Supports streaming and P2P traffic so you can access geoblocked content and torrent files safely.
Privacy Warning: These Popular VPNs Log Your Data
ThunderVPN
ThunderVPN’s privacy policy shows that it collects a significant amount of user data. This includes your ISP, OS version, device language, device model and manufacturer, amount of data transferred daily, connection times, and more. While VPNs have to keep some logs to run their service properly, storing information like individual connection times is invasive.
Hola VPN
Hola VPN clearly states in its privacy policy that it logs personal information, including but not limited to: your IP address, the web pages you visit, time spent on a website, and the dates and times you use the service. It retains this data for as long as it “deems it necessary.” The VPN also doesn’t encrypt internet traffic, which puts you at risk of being hacked. While there are decent free VPNs better than Hola VPN, the safest option remains a premium no-logs service like ExpressVPN.
Browse anonymously with ExpressVPN
FAQs: Importance of No-Log VPNs
What does a no-log VPN really mean?
“No-log” means that the VPN provider doesn’t keep any records of user activity whatsoever. The best no-log VPNs won’t store any identifiable information on your use of their service.
Creating a thorough no-log policy can be a complex task for most VPN providers, especially when they must also impose limits on time, data usage, or the number of devices. However, there is a general consensus that VPNs should avoid storing any user-identifying information beyond a short period after the VPN server connection ends.
Do all VPNs keep logs?
No. Admittedly, even premium no-log VPNs may keep some form of user information for optimal service delivery, but these are typically harmless logs. Reliable no-logs VPNs don’t store invasive usage logs such as the sites you visit, or connection logs like your IP address.
ExpressVPN is a good example of a no-log VPN. It doesn’t store your usage logs or IP address. And the limited connection logs it keeps are anonymized and aggregated, so activity can’t be traced to any particular user. ExpressVPN also has a 30*-day money-back guarantee, so you can try it out risk-free.
Why do VPNs keep logs of user data?
Even reputable VPNs store some logs to improve their services. For example, they may require an email address and payment details to set you up on a paid deal and to prevent fraud. Connection logs also help with troubleshooting issues as you use the service. Sometimes, VPNs have to store user data to comply with government regulations.
The issues arise when VPNs, especially free VPNs, keep logs to enforce bandwidth, time caps, and device connection limits. While storing some form of connection logs is understandable, keeping usage logs is invasive. Some dubious VPNs log your browsing habits to sell to third-parties such as advertisers. If a VPN stores usage logs, or too many connection logs, you should rethink using its service.
What’s the benefit of a no-log VPN?
A no-log VPN protects your online privacy and keeps your data safe from hackers and government surveillance. It gives you secure and anonymous access to the internet.
To ensure that your data is handled appropriately, it is crucial for your VPN provider to have a transparent privacy policy. Ideally, the policy should explicitly state that they do not log any of your data, as their primary function is to encrypt your internet traffic. Storing any form of details would be contradictory to this purpose.
Are there any free no-log VPNs?
No, there aren’t any free no-log VPNs. Even the best ones store connection logs like timestamps to help them enforce data limitations. Some free VPNs make money by selling records of your browsing activity to third parties.
Free VPNs also typically have weaker security features, don’t support torrenting, and can’t access geo-blocked content. Rather than use a free VPN that puts you at risk, go for a premium option like PrivateVPN, which has affordable monthly offers.
A No-Log VPN Remains Your Best Bet for Online Privacy
The purpose of a VPN is to protect your online privacy, and its log policy should show how well it secures your data. If a VPN stores logs that can be used to identify you, it’s not worth using. The first step to ensuring your privacy remains intact is to use a VPN service with a trustworthy no-log policy.
The VPNs on this list are strictly no-logs. ExpressVPN, in particular, has a verified no-logs policy backed by real-life incidents where the VPN couldn’t provide user data despite government orders. It has advanced security features like an automatic kill switch and AES 256-bit encryption, and runs its own DNS on all servers. You can try ExpressVPN totally risk-free. It has a 30*-day money-back guarantee, so you can get a full refund if you’re not satisfied with the service.
Browse anonymously with ExpressVPN
*Please note that ExpressVPN’s generous money-back guarantee applies to first-time customers only.
Summary — Best No-Log VPNs in 2026
Editor’s Note: We value our relationship with our readers, and we strive to earn your trust through transparency and integrity. We are in the same ownership group as some of the industry-leading products reviewed on this site: ExpressVPN, CyberGhost, Private Internet Access, and Intego. That said, our detailed reviews follow a strict methodology that examines all relevant performance factors to help you arrive at your own informed conclusion.











Leave a Comment
Cancel