Data Breach: Hundreds of Thousands of Customers’ Personal Information Exposed
WizCase’s security team, led by Ata Hakçıl, has found a major breach in popular online retailer Cosmolog Kozmetik’s database. This breach exposed users’ names, email addresses, physical addresses, phone numbers, order details, and more. Hundreds of thousands of users were compromised in the breach. There was no need for a password or login credentials to access this information, and the data was not encrypted.
What’s Happening?
Cosmolog Kozmetik is a Turkish online retailer and operates on almost all of the major Turkish e-commerce platforms including Trendyol, Hepsiburada, and Unishop. They are owned by Gercek Kozmetik. The company primarily deals in the sale and shipping of beauty products such as skincare and perfume. They also sell other goods under the name “Marketlog.”
Our team of ethical cyber researchers discovered an exposed Amazon S3 bucket belonging to the retailer containing over 9500 files and totalling almost 20GB of data. We tried to reach out to Cosmolog Kozmetik several times but received no response. We contacted the Turkish CERT as well as Amazon (hosting) a few times. At the time of writing, Cosmolog’s website wasn’t accessible.
What Data Was Exposed?
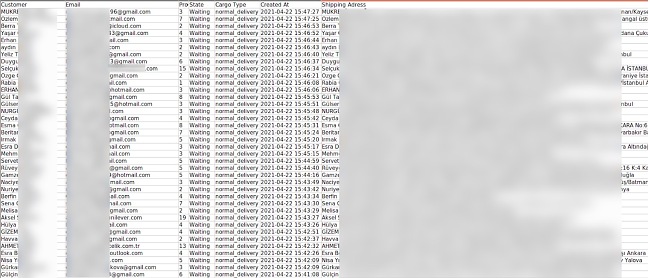
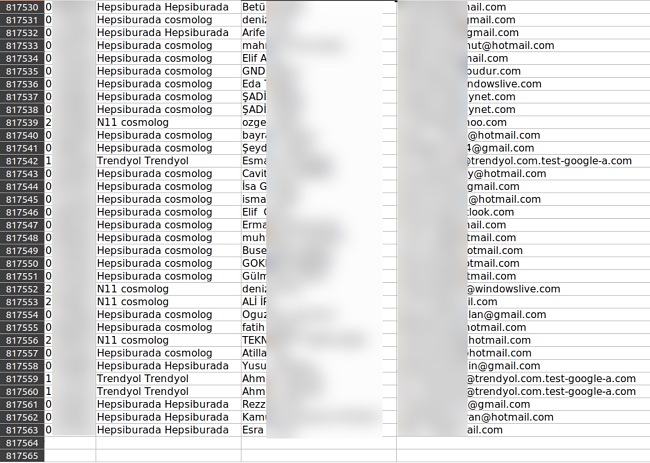
Cosmolog Kozmetik’s data breach made accessible over 5400 Excel files which exposed over 637,000 unique orders made by over 567,000 unique users on multiple e-commerce websites. The leaked order records revealed customers’ names, surnames, physical addresses, and purchase details such as items purchased and quantity of items. However, no payment information such as credit card numbers were found in the data breach.
In some cases, users’ phone numbers and email addresses were exposed too. The user details exposed were dependent on the platform the customer used to purchase items from Cosmolog Kozmetik. The amount of data available by user varies according to what the sites were sharing with Cosmolog. Below is a table of platforms the company operated on and what details were exposed on which platform:
| Website | Names and Surnames | Physical Address | Email Address | Phone Number | Payment Information |
| Cosmolog’s Website | Yes | Yes | Yes | Yes | No |
| Unishop Unilever | Yes | Yes | Yes | Yes | No |
| N11 | Yes | Yes | Yes | Yes | No |
| GittiGidiyor | Yes | Yes | Yes | Yes | No |
| Hepsiburada | Yes | Yes | Yes | No | No |
| Trendyol | Yes | Yes | No | No | No |
The orders were being updated frequently. The oldest files dated back to September 2019 and the earliest were being updated and the earliest were still being updated as we discovered the breach. The bucket also contained over 4000 images, almost all of them being product pictures from their website, while others were pictures from cancelled orders (mostly damaged goods) taken by Cosmoslog’s staff.
Cosmolog’s parent company, Gercek Kozmetik, has a close relationship with Unishop’s parent company, Unilever. Cosmolog is even listed as a co-responsible on Unishop’s privacy page. This is why there was more information exposed from Unishop than from, say, Hepsiburada and Trendyol.
The greater danger of this breach comes from Cosmolog Kozmetik’s use of multiple e-commerce platforms. Many users on these Turkish sites don’t check the name of the seller when purchasing goods and might not be aware of their exposure. If you purchased goods from Turkish platforms such as Trendyol or Hepsiburada, it is important you check who sold you those products. If you bought any Cosmolog Kozmetik or Marketlog products, you might be at risk.
What Are the Risks and How to Protect Yourself
Phishing: With a large number of PII (personally identifying information) exposed, conmen and unethical hackers might attempt to contact users with emails attempting to direct users to malicious websites where their credit card details can be stolen. The more information they have, the more trustworthy these emails can seem. For example, a bad actor could use the information exposed above to pose as a Cosmolog representative or a representative from one of the online e-commerce platforms in order to convince you to give them your payment details.
Frauds & Scams: The exposure of order details means bad actors can use common fraud tactics, such as refund scams, to steal money from Cosmolog Kozmetik or their customers.
Theft: Exposed PIIs such as names and physical addresses can allow bad actors to track shipments to users’ addresses and steal shipments as they arrive.
Unfortunately, the above list is not comprehensive, and cybercriminals are always generating new methods to exploit anyone vulnerable on the Internet.
For future purposes, we recommend always inputting the bare minimum of information when making a purchase or setting up an account on the Internet. The less information you give hackers to work with, the less vulnerable you are to attack.
Though most email clients have methods to block spam and phishing attempts, they are not 100% effective. When receiving an unexpected email from a seemingly trustworthy source, do not open any attachments. Phishing emails often use scare tactics to force users to open the attachment. If you are ever unsure about an email from a trustworthy company, give them a call. This will usually let you verify whether the attachment is legitimate or not. A good antivirus program can also aid in protection from malware, trojans, and other dangers.
In cases of potential theft, vigilance is necessary. If someone shows up at your door unexpectedly and claims to represent a certain company, always call the company and verify their claim.
Why Should I Trust WizCase?
WizCase is a widely popular web security platform offering advice and tips for thousands of readers every week. Translated into over 30 languages, our website has gained the trust of a wide number of people worldwide. Our team regularly discovers new data breaches across the internet and contacts them to companies responsible for them prior to publishing any reports. We have found breaches affecting many different companies from news websites, popular dating apps, and the medical industry. Together, we’re working hard towards creating a safer online environment for everyone.




Leave a Comment
Cancel