American News Site’s Subdomains Left Open for Takeover
Wizcase hacktivist team led by Avishai Efrat has recently found a vulnerability on an American broadcasting and media company website, CBS Local. Due to a technical misconfiguration, the content of 3 subdomains owned by the site became unregistered and open for takeover. Such vulnerability can be easily exploited by cybercriminals to trick users and steal their personal data or used to attack them in various other ways. Though the team has claimed and secured all 3 subdomains, CBS is still yet to respond to our messages and permanently remove the open mappings.
What’s Going On?
Subdomains are a prefix to a site address (URL) and are used by their parent (main) sites for technical or SEO-related reasons. So if a parent URL looks like www.parent.com, its subdomain could be found under www.subdomain.parent.com. Subdomains are set up for various different reasons, such as testing new features before they’re added to their parent URL or to separate between different types of content. Unfortunately, oftentimes they become vulnerable to takeover due to several reasons, like DNS and hosting misconfigurations or expired settings.
Many main sites host their subdomains’ content through external services, like Amazon Web Services (AWS) or GitHub. It enables main sites to upload and manage their content independently through an external host. It’s a useful practice for the parent site (in this instance, CBS Local) to be a part of the subdomain and appear internal.
Despite the benefits that come with using external host services, it often leads to subdomains becoming abandoned if they’re not removed properly by their owner. That can happen if the parent site cancels the hosting service, but doesn’t remove the subdomain mapping. It could allow anyone who finds the mapped subdomain to get access and rights to manage the subdomain’s content without permission. This is known as a subdomain takeover — a dangerous practice, often used to distribute malware, exploit user data, or used for phishing, stealing cookies, and more.
Our team of cybersecurity experts discovered 3 vulnerable subdomains that used to host different CBS Local content — ESP Guide, Contest, and Privacy Offers. Through extensive research, we found out that each subdomain held different types of content. According to our research, contest.cbslocal.com was used as a placeholder for displaying information about contests held by the main site. It’s possible it was a part of the company’s marketing strategy. Meanwhile, espguide.cbslocal.com served as a CBS newsletter called “Eat. Sleep. Play.” Finally, it seems that privacy.offers.cbslocal.com used to display CBS Local Privacy Policies. This last subdomain poses the best opportunities for scams as its name seems like a genuine privacy-related website.
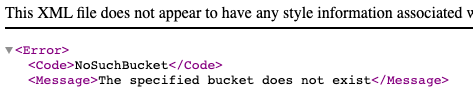
These subdomains point to URLs hosted on Amazon Simple Storage Service (S3) static website buckets. Unfortunately, the content of all 3 subdomains became unregistered at Amazon at some point while their content mapping remained active. This resulted in each site generating a “The specified bucket does not exist” error when approached. It’s a clear indication that a subdomain is vulnerable to takeover by anyone who comes across it.
How Did This Happen and What Does It Mean for CBS Users?
Despite the content being hosted on Amazon S3 buckets, it’s important to mention Amazon is not at fault here.
The vulnerabilities appeared because CBS Local didn’t cancel its existing content mapping but stopped using Amazon services. The 3 subdomain URLs were still working and registered on Amazon, therefore anyone could easily claim the buckets and control each subdomain.
Though the CBS Local website is visited regularly by millions of users, these subdomains seem to have been unregistered and empty for many years. The main website doesn’t link to any of them anymore, so it’s unlikely any CBS user was browsing through them. However, it doesn’t decrease the risks involved with a subdomain takeover. These vulnerabilities could still pose a great threat to unsuspecting users.
The main threats that come from using hijacked subdomains include:
- Phishing and scams: Very often, cybercriminals use a subdomain to create a duplicate of a well-known website to encourage users to input their personal data, account credentials, or even payment details. Such information, complete with your website activity, can be utilized in creating seemingly trustworthy phishing emails. Claimed subdomains are also used to persuade unsuspecting visitors to download malware or visit malicious websites.
- Main site cloning: Using a clone of the subdomain’s main site can be used to gain users’ trust and trick them into entering their personal details without suspecting anything. Then their data is used for various, usually malicious, purposes. Alongside phishing and scams, it’s the biggest threat to user data since it creates an easy way to deceive anyone who visits the hijacked subdomain.
- Site defacement: Claimed subdomains allows anyone to upload various forms of static content to them. Unfortunately, due to lack of external control, it can include offensive or unsettling materials such as extremist religious views, political outlooks, or fake news.
- Cookie data theft: Cookies are used to track and store user online activity on both main sites and their subdomains. As cookies are often shared between the domain and its subdomains, hijacking a subdomain gives attackers easy access to all the cookie data collected. This increases the chances of creating successful phishing attempts, scams, or may even lead to user identity theft. Although it’s not an active threat in this case (CBS Local and its subdomains weren’t configured to share cookies), cookie data theft is still a possible threat related to subdomain takeover.
- Malicious online attacks: Through the use of cookies and scripts, attackers can monitor users’ activity on the hijacked subdomain. This knowledge can then be used to increase click-throughs to dangerous websites or encourage users to download malware. On top of that, cybercriminals can hijack the main site by sending HTTP requests and running malicious Javascript on the subdomain.
It’s important to remember that all Amazon static websites (such as the vulnerable subdomains mentioned) don’t have any server-side capabilities. This means these sites don’t participate in any back-end processes, such as logins and database communication. However, any static website can be used to redirect an unsuspecting user to unsecure sites that collect such content. Alternatively, attackers can run malicious client side scripts using Javascript on the vulnerable domain.
Do I Need to Do Anything Now?
Our cybersecurity team successfully claimed and secured all 3 vulnerable subdomains. As a proof of concept (POC), they then uploaded unharmful static content to discourage hackers from hijacking them. As soon as these vulnerabilities were discovered, we also contacted CBS Local. Once we receive a reply, we’ll be able to hand the subdomains over so they can be permanently removed.

Even though these vulnerabilities are now secured, it’s very likely there are many other unregistered buckets like the CBS ones. News reports show that many big companies, like Microsoft, Amazon, and Apple, also had their subdomains hijacked. Unfortunately, in many instances, users’ credentials are stolen or misused as a result.
Luckily, you can still protect your personal information online and avoid having your data harvested.
Refrain from entering your personal details on any site without a secured HTTPS address. Make sure the site doesn’t display any certificate errors either. Should you come across a site or its subdomain with a suspicious HTTP address, avoid clicking on any pop-up ads or prompts. They can be infected with various types of malware or viruses, ready to be installed on your device with just one click.
Remember to report anything suspicious as soon as you see it, including unusual emails or shady site functions. That way you will protect not only your own data but also prevent other users from being scammed.
For extra protection, install a trustworthy antivirus program and a VPN. They will add an additional layer of security to your device while protecting your online identity. You can even try many VPN providers for free for a certain period of time, completely risk-free! To learn more about how a VPN protects your online data, follow our VPN guide for beginners.
Why Should I Trust WizCase?
Translated in nearly 30 languages, WizCase is one of the leading websites concerning online freedom and internet safety. Our website helps people across the globe and gained thousands of regular readers very quickly. We regularly discover and report new data breaches and website vulnerabilities, such as multiple leaks in the medical industry and unsecured servers on a popular culinary site.
Prior to publishing each report, we always contact the affected company to inform it about the existing issue. This ensures the leaks or any vulnerabilities can be secured to protect exposed data and users involved.
Although we’ve contacted CBS Local multiple times to make them aware of the issue, we haven’t received a response yet. We hope that by publishing this report, we can encourage the company to secure the vulnerable subdomains themselves. Until then, our POC should prevent any hackers from trying to hijack the subdomains.




Leave a Comment
Cancel