Popular Celebrity News Site’s Subdomain Vulnerable to Takeover
WizCase has discovered a vulnerability on a widely popular website with up-to-date celebrity news, People.com. The site had an open and working subdomain available for potential takeover. If claimed by cybercriminals, such vulnerability would serve a perfect opportunity for phishing, scams, or even identity theft. Our team of experts has since secured the vulnerability, but the company was slow to respond to our warnings and remove the subdomain completely, only doing so recently.
What’s Going On?
A subdomain is an independent domain that is a part of another parent domain, for example childDomain.parentDomain.com. They are usually used to differentiate content that’s separate from the main website or relate to it in different technical aspects, like Single Sign-On (SSO). Using a subdomain can also provide a way of testing a newer version of the site before publishing on the more widely available platform. Finally, many popular online stores create a subdomain to handle their transactions using 3rd parties as eCommerce sites are usually more complex to create.
To serve their content, subdomains are commonly hosted through external services and companies, such as Amazon Web Services (AWS) buckets, Azure, GitHub, and more. However, if the main site stops using the external service, but doesn’t cancel the subdomain, the existing link continues to work redirecting online users to an empty site. This means that anyone who finds the abandoned external service and claims it can upload any content to the empty subdomain. Very often, subdomain takeovers are used to deploy malware or tricking its users to enter their personal details. From there, they can exploit people’s online data through phishing, scams, and identity theft.
Our cybersecurity team came across a vulnerable subdomain belonging to People.com, called AmericanDream. The subdomain’s content was already removed, however, our research revealed the site used to hold different American “Against the odds” stories of famous and successful people. We also found scarce details about an ebook that seems to have been available on the site.
When we approached this People.com subdomain, we discovered its content was mapped to an Amazon Simple Storage Service (S3) bucket. Using buckets provides a way to upload static content to a specific URL and host it on Amazon’s public cloud storage space. This allows the main website (in this case, People.com) to still own and manage the subdomain independently but through the external host.
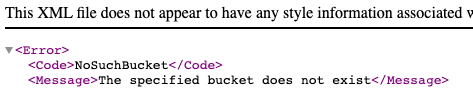
The subdomain takeover vulnerability happens when this mapping stays active but the content on its external service provider (in this instance, the Amazon bucket) becomes unregistered. That’s why the People.com subdomain displayed an Amazon-specific “The specified bucket does not exist” error as soon as we tried to open it. This vulnerability would allow anyone to create a new bucket with the same name and, in effect, change the contents served on americandream.people.com.
How Did This Happen and What Are the Consequences?
The issue with People.com subdomain vulnerability stems from the news platform not removing its existing mapping of the subdomain to Amazon when they cancelled the external service. As the URL redirection was still registered and working, anyone who found it could claim the bucket URL in AWS S3. That unauthorized access would allow the new host to take control of the subdomain and use it to exploit people’s personal data.
It’s important to note that Amazon is not at fault here. It was People.com’s responsibility to make sure its subdomain was properly closed.
The main risks of subdomain takeover include:
- Cookie data theft: Every time a user visits a website, their activities are usually tracked and stored within the site’s servers through the use of cookies. In case of a hijacked subdomain, all that collected data becomes visible to the attacker and may be potentially stolen. This would increase users’ vulnerability to phishing attempts, scams, and even identity theft. Though not possible in this case as People.com and its subdomain weren’t configured to share cookies, cookie data theft is a common risk involved with subdomain takeover.
- Phishing/scams: Gaining control over subdomains is widely used to create more believable phishing scams. Through cloning a trustworthy website with a seemingly secure HTTPS connection, attackers can trick visitors into providing their personal account credentials or credit card information. It can also be used to encourage click-throughs to malicious third-party links.
- Malicious attacks on site users: Cybercriminals can easily track and monitor users’ activity on the vulnerable subdomain. It can also be used to convince site visitors to download malware or click on links redirecting them to dangerous websites. Additionally, hackers may run malicious Javascript on the subdomain to compromise users’ privacy or send HTTP requests in an attempt to bypass security restrictions on the main site.
- Cloning main site: Hackers can use the subdomain to create an exact copy of the trustworthy main site to redirect its users. This copy can be used for a variety of purposes, including increasing link clicks, encouraging malicious downloads, or collecting personal data from every visitor.
- Site defacement: Anyone who gets hold of and claims the subdomain can then start uploading any static content they want to the site. This very often includes harmful materials such as extremist political or religious opinions, fake news, and pornography.
Additionally, despite the external provider service being a static website (which means it doesn’t have server side logic, such as a login process or a database), it could still be used by hackers as a resource to redirect attackers to such server content due to its connection with the main site.
It’s crucial to remember that this list is not exhaustive and there is a possibility of other additional risks of such vulnerability.
Is There Anything I Need to Do Now?
Our team of white hat hacktivists successfully identified the issue and claimed the vulnerable bucket. They then proceeded to upload an unharmful static content as a proof of concept (POC). This prevented anyone unauthorised from hijacking the domain from that time. We’ve also contacted People.com and Amazon to make them aware of the issue. The issue was recently resolved, thus removing the vulnerable subdomain altogether.

Though this subdomain vulnerability is now secure, there are many other buckets that could be taken over. In the past, many big online platforms, like Slack, GiHub, and Uber, had their expired subdomains hijacked and their users’ credentials were stolen as a result.
Unfortunately, there isn’t much you can do as a user to protect your data in case of a subdomain takeover. It’s a company’s responsibility to constantly monitor its online platform for unauthorised DNS entries. However, there are still certain precautions you should take to minimise the risk of having your data harvested.
Always be vigilant and check for signs of suspicious subdomains. These include, but aren’t limited to, a website displaying certificate errors or showing an unsecure HTTPS address.
Don’t enter your personal details if you’ve never had to do that before, even if the site prompts you with a pop-up message. Trustworthy sites would never ask for additional information if you used the service already.
If you’re browsing through any unsecured sites or their subdomains, refrain from clicking on pop-up warnings or ads, especially if it means you’ll need to download something. They are often riddled with malware that creates a backdoor for hackers allowing them to take control of your device or steal your data.
If you come across any unusual activity tied to your name or unknown files on your device, report it as soon as possible.
Finally, make sure you use a reputable antivirus software, as well as a VPN provider. Both programs will protect you against phishing, malicious downloads, or identity theft. Various providers offer their services for free, so you can stay safe without going over your budget. To learn more about how a VPN can help you, read our VPN guide for beginners.
Who Is WizCase?
WizCase is a leading virtual security website specializing in VPN protection, but also guides and tips on how to increase your online security. With our articles translated in 29 languages, we regularly help increase online protection for people all over the world. Our team regularly uncovers data breaches and security issues, including recent e-commerce website leaks and potential spyware on webcams.
We always ensure the company involved is aware of security issues before publishing our reports. That way the problems can be fixed quickly to protect its users from any cybercrimes.
We’ve disclosed the issue to both People.com and AWS, but so far, nobody responded to our messages. To thwart the risk of website hijacking, I personally took action to seize and fortify the subdomain once we unearthed the vulnerability. This step was aimed at preventing any malicious exploitation of it. It appears that the companies have since resolved the problem.



