Data Breach: Around 9,500 Apartment-Sharing Site Users Affected
WizCase has uncovered an open Amazon S3 bucket on an American apartment home-sharing platform, Niido. The leak exposed over 9,500 users’ personal information, including full names, email addresses, and phone numbers. We have contacted the company, Amazon, and the US CERT to disclose the issue. It was secured following a second reach out to Amazon’s team who informed their customers.
What’s Happening?
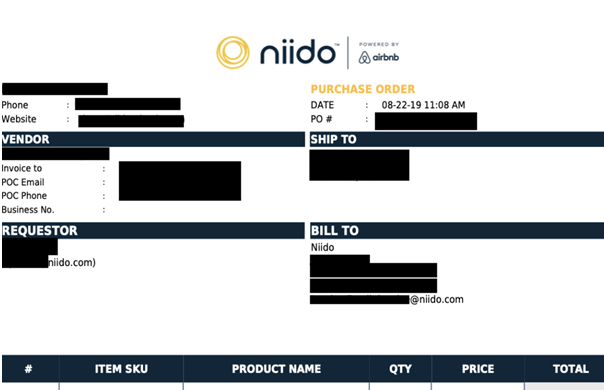
WizCase research team found a data breach related to Niido, an American online apartment house-sharing website. Niido also stores certain user data that can be linked with Airbnb as both platforms have announced their collaboration in 2018. Despite that, Airbnb is in no way related or responsible for the leak. The open Amazon S3 bucket was used to store 2 CSV files with between 20-30MB of user data and around 300 PDF documents.
The breach exposed personal data of users and property owners registered on Niido, including:
- Full names
- Email addresses
- Phone numbers
- Airbnb internal guest email
- Internal booking information
- Data about the property owner and area
- Booking confirmation codes
- User reviews data
- Direct comments from house owners to cleaners

The open bucket also revealed around 300 PDF files with invoices for orders made by the company.
Whose Data Is Affected and What Are the Consequences?
Our team discovered that the misconfigured bucket had 2 CSV files with between 20-30MB of data with around 9,500 Personal Identifiable Information (PII) and a few hundred confidential files. The data included some duplicate information and empty values. According to the names of the files, all exposed data belongs to registered AirBnB users — both guests and hosts.
An additional CSV file with 2,000 entries showing full names, confirmation codes, and user reviews score was also found within the bucket.
Allowing public access to an open Amazon S3 bucket is an unacceptable breach of privacy that could lead to various scams and online dangers. Any user who had their data exposed in the breach is now facing several security threats, such as:
- Identity theft and fraud: The breach exposed data that could be easily used by cybercriminals to perform identity theft. Possible fraudulent activity would be for attackers to create new host accounts with fake images and property details. Doing so would allow them to collect payment details, money, and personal details of their unsuspecting victims.
- Phishing scams and malicious emails: Scammers are always on the lookout for data breaches to collect various parts of private information. Knowing a person’s full name, phone number, and their recent Airbnb transactions could aid in creating believable phishing emails. These are sent out to collect additional data from the victim by attaching suspicious links in emails. Additionally, attackers could use leaked email addresses to spread malicious files that, when downloaded, infect the person’s device.
- Business espionage: Various Airbnb and Niido competitors could use revealed information to convert users to switch to their platforms. This could be done by ad targeting and sending them new offers through emails and text messages. As these could be highly personalized, many espionage attempts are likely to be successful.
How Did It Happen and What Shall I Do Now?
Amazon S3 buckets are an extremely popular cloud-based storage solution used by various online companies. By default, S3 buckets are private, yet many admins change their security permissions to public as they aren’t aware of the implications. Very often, they also don’t have an appropriate understanding of how to reverse these settings or forget to do it at all. It’s something many companies tend to overlook. Unfortunately, cyber attackers look specifically for these types of misconfigurations as it happens to an increasing number of businesses nowadays.
Unless intended to be accessed by the public, any server and bucket used to hold user personal data should be set to private. This would significantly lower the chances of a data breach happening.
It’s important to mention that Amazon is not responsible for the leak — it was the responsibility of the company’s admins to make sure the misconfigured bucket was secure.
If you regularly use your Airbnb or Niido account, delete unnecessary information on your profile and limit the data you share in the future. You should also be aware of any phishing emails or phone calls that ask you to share more personal information.
Should you notice any suspicious activity or unknown changes on your accounts, report it as soon as possible.
As a general rule, it’s a good idea to protect your online traffic by connecting to a VPN. This adds an additional layer of protection to your data through masking your IP address as well as preventing any malware from attacking your devices. VPNs are very easy to navigate through, even for those who never heard of them before — for an easy tutorial check out our beginner’s guide to VPNs.
Who Is WizCase?
Available in over 30 languages, WizCase is an online security website that reaches millions of readers worldwide. Our team always reaches out to any platform involved in data leaks and breaches as soon as the vulnerability is discovered. This is done prior to publishing any report in order to ensure the breach is secured and the users whose data was exposed are safe from any harm.



