What is IPv6 and Why You Should Care
IPv4 and IPv6 are technical terms used quite often regarding VPNs, cybersecurity, and online computing in general. While these terms are crucial to understanding how internet traffic works, few people have a proper understanding of what they mean.
If you’re in the dark about the definition of IPv6, you’re in the right place. With IPv6 on its way to becoming the norm, now is the time to understand what it is, and why you need to know about it.
What is IP?
The initials “IP” stand for “Internet Protocol” and refer to a specific set of rules for how data is transmitted over a network. Hence why a web address is also known as an IP address. These protocols create a standardized language for how devices communicate online.
Routing is one of the main functions of the IP, which is defined as forwarding data packets from source to destination machines over a network, determined by their addresses.
The vast majority of networks combine IP with Transmission Control Protocol (TCP); an action that facilitates a connection between a destination and a source, allowing them to send messages back and forth while the link is established.
Versions of Internet Protocol
Currently, there are two versions of internet protocol:
- IPv4
- IPv6 (the more recent)
What is IPv4 (Internet Protocol Version 4)?
To send data from one device to another on the internet, it must be transferred across a network that contains the IP addresses of both devices. IPv4 currently allows us to connect our devices to the web, and it’s been the norm since 1983.
IPv4 is a 32-bit decimal number containing four number strings, each two to three digits, identifying your device and location.
A typical IPv4 address appears like this: 192.168.0.1
Currently, IPv6 coexists with IPv4. However, IPv6 will become the standard eventually. The upgrade is necessary mainly due to the finite amount of IP addresses available with IPv4.
If you want to look up your IPv4 address, you can do that here.
What is IPv6?
Internet Protocol Version 6 is the most recent network layer protocol; systems which allow communication to transfer over a network. Although conceptualized in 1998, it only began to replace IPv4 in 2017.
Why Do We Need IPv6?

When IPv6 first started to be developed, the expectation was that by 2010, all variations of unique IPv4 addresses would be in use. In response, a new network layer protocol was created to allow additional unique addresses, and that was the start of IPv6.
Wait. Why are we Running out of IPv4 Addresses?
Since IPv4 uses 32 bits for IP address, that means there’s a maximum of around 4.29 billion potential variations. While that sounds like a lot, in the grand scheme of things, it’s not. In fact, all IPv4 addresses have already been designated to several different institutions.
Although these addresses have already been taken, a significant portion of them are not in use and sit idly despite being owned by institutions like MIT, and companies like Chevrolet, and Dell.
So, as it currently stands, IPv4 addresses can still be purchased and assigned, but the numbers will continue to dwindle over the next few years, which will create issues. Initiating IPv6 resolves the problem.
The Difference Between IPv4 and IPv6 Addresses
IPv6 is the successor to IPv4 and has been designed to enable the Internet to grow at a steady pace in regards to the number of hosts connected and the total amount of data traffic transmitted.
There are technical differences between the two, but the most distinguishing and essential difference is the length of the addresses themselves. IPv6 is a 128-bit decimal address consisting of eight groups of four digits. The full address can be abbreviated, but the potential for addresses is expansive compared to IPv6.
A typical IPv6 address appears like this: 2018:0ab6:84a2:0000:0000:7a2b:0271:7435
Types of IPv6 Address
There are three types of IPv6 address.
- Unicast – one-to-one communication. A single source is transmitting data to a single destination.
- Multicast – one-to-many communication. A transmission is received by a group of devices as the destination.
- Anycast – similar to multicast, however, the source chooses the closest destination of many for transmission.
The Benefits and Advantages of IPv6
Advantages:
- More available addresses
- Improved connectivity in P2P networks
- Faster speeds
- Auto-configuration
- Routing efficiency
- Strong security
- Higher conversion rates
Disadvantages:
- IPv4 remains more popular
- IPv6 and IPv4 can’t communicate directly and requires a server
- VPN providers have been unresponsive in upgrading servers to support IPv6
Due to the many advantages of IPv6, the majority of network engineers, data centers, tech companies, and mobile carriers utilize IPv6. IPv6 is the preferred choice for professionals, and it should be for the average user as well.
The Current State of IPv6
IPv6 was launched in 1998, but the Internet as a whole has been slow to embrace it. In fact, most countries have less than 15% of their traffic going through IPv6 connections.
So why can’t we all switch over already?
Well, at this point, it’s due to the cost of the transition. IPv6 requires the use of new server software and equipment. Further complicating the switch is the fact that any website that wants to accommodate users with both IPv4 and IPv6 will either need two separate versions of their site or use a translation service, which is also costly.
Still, IPv6 is on the rise, as we have no choice but to make the transition slowly. Today, the majority of routers and operating systems can support it. ISPs are continually offering more IPv6 capabilities to their users.
How Will This Change Affect Me?
As of right now, this switch will not affect you all that much. After all, all the major operating systems support IPv6, like Mac OS X 10.2 and Windows XP SP 1.
With that said, there are still a lot of routers and servers that can’t support it. Still, the transition is a necessity, so expect things to pick up over the next few years.
If you use a VPN, there are some vital aspects you need to know about IPv6.
Should You Use IPv6 Right Now?
IPv6 certainly has a lot of advantages, and the widespread use of it is inevitable. But should you be using it right now, even though it’s not anywhere near being the IP of choice as of yet?
That all depends. If your ISP offers IPv6, and your router can support it, you should go ahead and turn it on, if it’s not already.
Depending on your OS, computer, or device, you may already be using IPv6, and you can run a test to see if you are. Just go to www.test-ipv6.com to know if you’re employing IPv6.
If you aren’t running IPv6 it will be dependent on your router and/or ISP. You can run a search for specific instructions by performing a query for “[router manufacturer] ipv6 [your ISP].” It’s also a good idea to upgrade your router’s firmware to DD-WRT as this will make the change much more manageable.
As of right now, there are two main ways to view IPv6 sites:
With the transition mechanism
Transition mechanisms encapsulate IPv6 data in IPv4 transmissions, which allows you to view IPv6 sites with an older protocol.
Natively
A native IPv6 connection allows for a direct link, with no transition needed.
If you’d like to see if a specific site will accept IPv6 connections, you can use this IPv6 validation tool. If the site has a 128-bit IP address, it’s compatible with IPv6.
Does IPv6 Leak Your Identity?
When using a VPN provider, you’re assigned an alternative IPv4 address which protects your privacy and provides online anonymity.
If you attempt to communicate with an IPv6 server, the VPN can ignore the request, redirecting the traffic via your ISP server. If this happens, you’re no longer obfuscated with the VPN encryption, and there’s a possibility that your real IP address might be revealed, exposing your identity.
Using the best VPN for iPv6 leak protection keeps you secure online.
Test Your VPN for an IPv6 Leak
Necessary tests are available online, but they don’t identify all problems like brief reconnection leaks, or similar issues. You need an advanced analysis to ensure your VPN utilizes the correct setup.
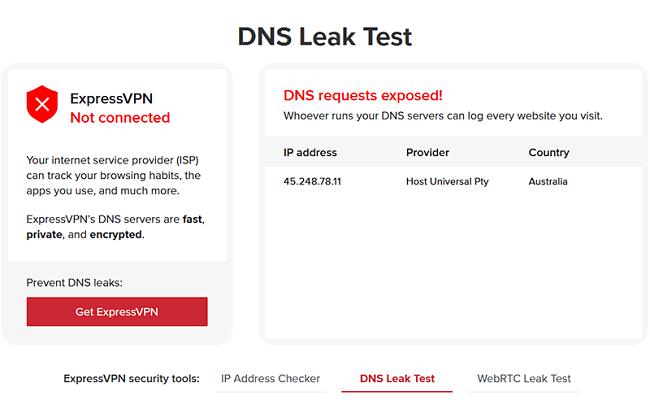
- Connect to a VPN server.
- Go to the IPv6 testing site and see if the IP address and location listed are yours or the VPN provided IPv6 and location.
- For an example of how the tunnel responds to interruptions; disconnect your WiFi or Ethernet cable while running the VPN. Then retest.
- Reconnect and load different websites while testing as well.
- If you recognize unusual readings while using a VPN, report them to the provider immediately.
If you don’t have ExpressVPN, you can use any of these testing sites using the same steps listed above.
How to Turn Off IPv6
To ensure privacy and anonymity until the stage where IPv6 is fully integrated, some people prefer to turn it off altogether. It is a simple process if you’re using Windows or Mac operating systems.
Windows
- Go to Settings > Network & Internet > Network & Sharing Center.
- Click Change adapter settings, and then right-click your primary internet connection. Now select Properties.
- Scroll down until you see Internet Protocol Version 6 (TCP/IPv6). Uncheck the box.
Mac
- Go to System Preferences > Network. Click Advanced, and go to the TCP/IP tab.
- Change the Configure IPv6 drop-down menu to Off.
Mac Terminal Command
Some Mac user may need to run a Terminal command.
To do this, open Terminal and run one of the following commands:
networksetup -setv6off “Ethernet”
This will enable the Off option in the TCP/IP tab of the Network settings. If you need to turn it back on, select Automatically in the menu, or run one of these commands:
networksetup -setv6automatic “Ethernet”
The Two Best VPNs that Protect Your IPv6
1ExpressVPN

- IPv6 leak protection
- No connection logs
- Unlimited bandwidth
- Access to over 3,000 server locations
- Easy-to-use interface
- 30-day money-back guarantee
Not only is ExpressVPN one of the fastest on the market, but they are also serious about security. They protect customers with 256-bit AES encryption, an automatic kill switch, and split tunneling.
Compatible with Windows, Mac, iOS, Android, and more, connection supports three multiple devices simultaneously, and there is 24/7 customer support.
2CyberGhost VPN
- DNS and IP leak protection
- Automatic kill switch
- No logging policy
- 256-bit AES encryption
- Unlimited bandwidth
- 45-day money-back guarantee
CyberGhost VPN provides an extensive global network with more than 3,000 secure servers.
Additional online security provided by the ad and malicious content blockers is a bonus, and a simultaneous connection is supported on up to seven devices simultaneously.
24/7 customer support is on hand for any issues.
Protect Yourself Online
Until IPv6 is organically integrated into all aspects of online communication, security, etc., we recommend this guide is used as a reference point of how to maintain privacy and anonymity.
Utilize any of the above VPNs to ensure that your online activity remains private. With one of our top 2 choices, you won’t have to worry about your security.
However, be aware that lapses can occur, and you should regularly test for leaks and update your software when available.



