Best Antivirus Software in 2024 for Windows, Android & More
Modern-day operating systems have strong built-in security measures, but cyber threats have become so advanced that these solutions don’t cut it. Even clicking one wrong email attachment can compromise your data. So, getting a top antivirus is crucial to protect your devices.
There are many antiviruses available nowadays, but only a few deliver reliable safety. So, I extensively tested numerous antiviruses and picked the best ones that can effectively secure any device. The apps I’ve picked offer excellent malware detection, useful security features, and more to ensure you’re protected against every threat.
Each of the antivirus solutions listed below effectively defends against advanced malware. However, Norton is my #1 pick, thanks to its impressive 100% detection score and generous 60-day money-back guarantee.
Try Norton risk-free for 60 days
Quick Guide: Best Antivirus Software in 2024
- Norton — #1 antivirus with flawless malware detection and many reliable security features.
- TotalAV — Provides beginner-friendly and easy-to-install apps, but its support isn’t the best.
- McAfee — Has a built-in VPN with AES 256-bit encryption for improved online safety, but its scans are slow.
- Intego — Offers an innovative 2-way firewall, but the Windows app is missing some features.
- Bitdefender — Includes many features to add extra layers of security, but it gets expensive after the first year.
- Plus 5 more great antiviruses that made the cut! Read more about them here.
- Jump here for a quick comparison table of the best antiviruses.
10 Best Antivirus Software (Tested 2024)
1. Norton — The #1 Overall Antivirus With Flawless Security
Quick Look: Norton Results
| Security | advanced — 100% malware detection, multiple scans, advanced firewall, phishing protection, ransomware protection, and web protection |
| Features | excellent — built-in VPN, parental controls, password manager, and encrypted cloud storage |
| Native apps | all main platforms — Windows, macOS, iOS, and Android |
| Device connections | up to unlimited (depending on the plan) |
| Customer support | 24/7 live chat, phone support, community forums, and an online knowledge base |
| Money-back guarantee | 60 days |
| Minor cons | ✘ gets more expensive when renewing |
| Best Price | $29.99/year |
I consider Norton the best antivirus you can get in 2024. It has flawless malware detection capabilities, many advanced safety features, easy-to-use apps for all major platforms, and reasonable price plans. Plus, its best-in-class customer support ensures you can get help whenever needed.
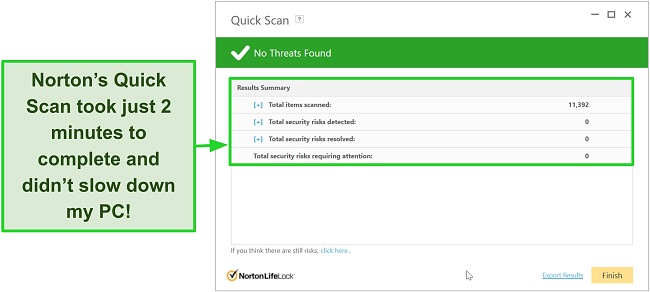
During tests, Norton’s scans reliably found and removed malware from my system with a 100% detection score. Plus, its quick scan only took 2 minutes to complete, while the full scan took only 20 minutes to look for threats across my whole system. Besides this, Norton has equally effective real-time security that blocks threats before they can infect your devices.
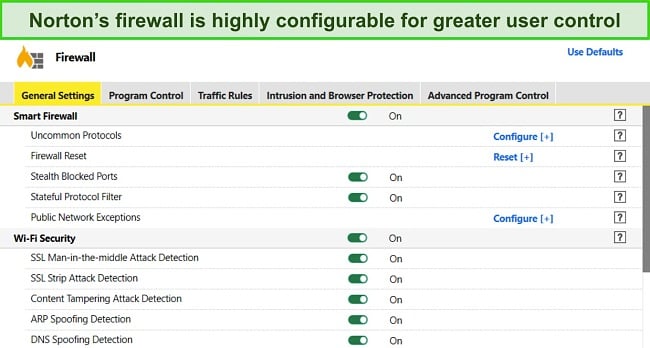
Norton has an excellent built-in VPN with AES 256-bit encryption and a no-logs policy for improved online safety. You’ll also get an advanced firewall with Norton that improves security. The firewall has many configuration options, but the default configuration also delivers excellent safety.
The app also includes an impressive variety of other safety features, which include the following:
- Dark web monitoring — checks if any of your accounts were leaked in data breaches.
- Parental control suite — helps safeguard your kids by monitoring and managing their online activity.
- Password manager — provides encrypted storage for your passwords and other sensitive data.
- Encrypted cloud storage — offers up to 500GB of secure storage (in the US) to hold all your sensitive files and other data.
- Software updater — finds and updates outdated apps on your system to patch vulnerabilities.
- PC SafeCam — blocks unauthorized access to your system’s webcam.
- Privacy monitor — locates and helps remove your data from people-search websites.
I was also impressed with Norton’s top-quality customer support. When I tested its live chat, I always connected to an agent within a minute, who proceeded to give helpful answers to any questions I had. Plus, Norton includes phone support, community forums, and an online knowledge base for additional help.
Norton is available for as low as $29.99/year. However, I found that Norton’s $49.99/year Deluxe plan delivers the best overall value. It includes the app’s core security features, built-in VPN, 50GB of cloud storage (in the US), and protection for up to 5 devices.
You can also try Norton without risk, as it provides a 60-day money-back guarantee. I even tested its refund policy, and the live chat agent instantly processed my refund when I asked. Afterward, I had the money back in my account within 5 days.
2. TotalAV — Beginner-Friendly Antivirus With Reliable Security
Quick Look: TotalAV Results
| Security | advanced — 100% malware detection via scans, 100% real-time malware detection, web protection, ransomware protection, and phishing protection |
| Features | excellent — built-in VPN, password manager, ad blocking, optimization tools, and a data breach test |
| Native apps | all main platforms — Windows, macOS, iOS, and Android |
| Device connections | up to 6 (depending on the plan) |
| Customer support | 24/7 live chat, phone support, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons | ✘ doesn’t have a customizable firewall ✘ more expensive after the first year |
| Best price | $19.00/year — free plan also available |
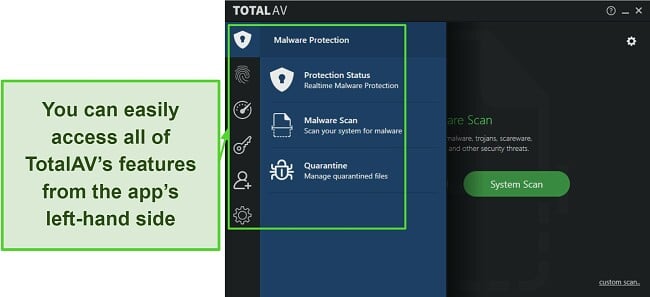
TotalAV’s intuitive and feature-packed apps help it stand out as a worthwhile antivirus. I found it easy to navigate TotalAV’s desktop and mobile apps to secure my devices with this antivirus’ various features. Plus, the desktop app has a helpful menu on the left-hand side that makes it simple to use any of the app’s features.
TotalAV’s security was very impressive during my tests. Its virus scans found and removed 100% of the malware from my system. Plus, it has reasonably fast scans, with the full scan taking roughly 30 minutes to check my system. Note that TotalAV doesn’t have a built-in firewall like other top antiviruses. So, it’s not as good as Norton for safety.
You’ll also get a Windscribe-powered VPN with TotalAV. Windscribe is a renowned name in the VPN industry, so it’s no surprise that TotalAV’s VPN is fast, secure, and reliable. It uses AES 256-bit encryption, and my connection speeds only dropped 10% compared to baseline values while connected to it. Plus, it has servers in 30+ countries.

Other useful features available in TotalAV’s apps include the following:
- Data breach check — checks if your accounts were leaked in data breaches.
- Total Adblock — blocks annoying ads and trackers for smoother and faster browsing.
- Total Password — offers secure storage for passwords and other sensitive data.
- System Tune-Up — cleans junk files, removes duplicates, and stops unnecessary startup programs to improve system performance.
TotalAV provides multiple plans that start at just $19.00/year. However, TotalAV’s $39.00/year Internet Security plan delivers the best value. It secures up to 5 devices and includes the app’s necessary features with a small jump in price.
You can even try TotalAV risk-free to see if it suits you. If the app doesn’t meet your needs, it’s easy to get a refund by contacting support. I had my money back in just 2 days when I asked for a refund by contacting phone support.
3. McAfee — Excellent Choice for Comprehensive Internet Security
Quick Look: McAfee Results
| Security | advanced — 100% malware detection score, ransomware blocking, advanced firewall, cryptojacking protection, web protection, and network protection |
| Features | excellent — Built-in VPN, file shredder, parental controls, password manager, and ID theft protection (US only) |
| Native apps | all main platforms — Windows, macOS, iOS, and Android |
| Device connections | up to 10 (depending on the plan) |
| Customer support | 24/7 live chat, phone support, community forums, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons | ✘ live chat is slow to connect and respond |
| Best price | $39.99/year |
McAfee offers comprehensive safety via its Global Threat Intelligence System that blocks malware before it can infect your devices. I was especially impressed with its WebAdvisor, which is a reliable web extension that blocks unsafe websites. It always informed me when I was about to open a malicious site that could infect my system.
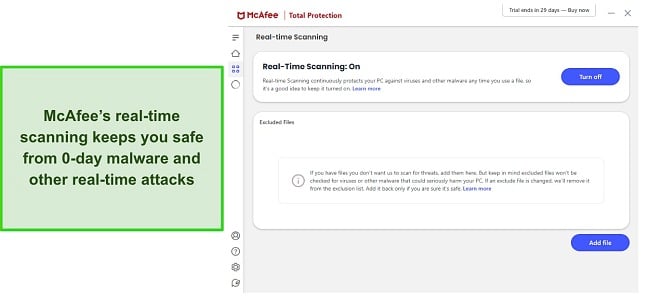
During tests, McAfee impressed a lot with its excellent malware detection capabilities. It found 100% of threats via its quick, full, and custom scans, and it offers equally effective real-time security to block zero-day malware and other threats. The only downside I noticed is that McAfee’s scans are slow — the full scan took more than 2 hours to check my whole system.
I like that McAfee’s firewall works alongside Windows’ built-in firewall to improve your overall security. Windows firewall blocks dangerous incoming connections, while McAfee’s firewall works to stop risky outgoing connections. Both firewalls working simultaneously leads to better overall protection.
You’ll also get other security features with McAfee, including the following:
- Password manager — stores your passwords and other sensitive information safely.
- File Shredder — shreds files multiple times to ensure they’re permanently inaccessible.
- Built-in VPN — secures your online activity with AES 256-bit encryption and keeps you anonymous.
- Parental control suite — helps monitor and manage your kids’ activity to keep them safe.
- ID monitoring — informs you about any breached accounts linked to your email.
- Tracker Remover — finds and removes trackers, cookies, and other unnecessary files.
- Protection Center — provides a security score based on your overall device safety.
While it’s not as good as Norton’s support, McAfee provides reliable customer support via live chat, phone support, community forums, and an online knowledge base. It’s easy to get help via any of these channels if you need it, and I found that the live chat is the fastest way to contact an agent for assistance.
McAfee has multiple plans to meet everyone’s needs, but I found that the $35.99/year Total Protection Plus plan is its best-value offering. It has McAfee’s core antivirus features, firewall, built-in VPN, web protection, ID monitoring, and protection for up to 5 devices.
You can even try McAfee risk-free, thanks to its 30-day money-back guarantee. After my tests, I tested the refund policy by asking for a refund via McAfee’s phone support, which the agent confirmed immediately. I had the money back in my account 7 days later.
4. Intego — Top Antivirus for macOS Safety
Quick Look: Intego Results
| Security | advanced — 99.4% malware detection, effective real-time security, and 2-way NetBarrier firewall |
| Features | average — Secure browsing, parental controls, Mac Washing Machine, and personal backup |
| Native apps | desktop-only — Windows and macOS |
| Device connections | up to 5 |
| Customer support | live chat, email support, phone support, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons |
✘ Windows app is limited compared to the macOS app ✘ live chat isn’t available 24/7 |
| Best Price | $19.99/year |
I consider Intego the top macOS antivirus available, and it even offers a Windows app. It’s a reliable antivirus that secures against even the most sophisticated macOS threats with its impressive malware detection. Plus, it has excellent extra features and is lightweight, meaning it won’t slow down your device at all.
During tests, Intego reliably found most malware with a 99.4% detection score. It’s not flawless, but it’s much better than the 85% average for macOS antiviruses. I also like that Intego is equally effective at detecting malware on Windows devices, meaning it’s a good choice for households that have devices on both platforms.
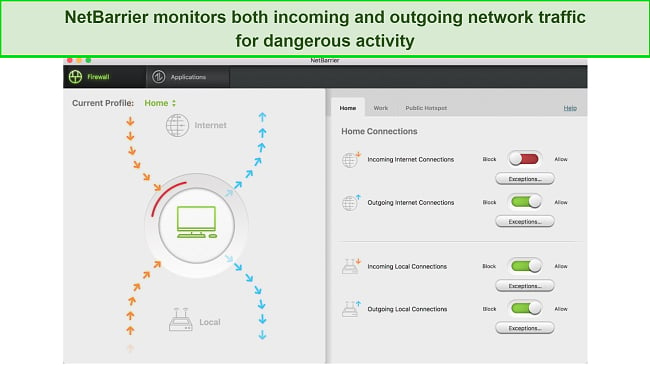
Another Intego highlight is the innovative NetBarrier firewall. Intego’s NetBarrier has a 2-way design that monitors incoming and outgoing traffic. This helps ensure no cyber threats can infiltrate your network and start harming your devices or stealing any sensitive data. Unfortunately, this firewall is only available in Intego’s macOS app.
Some other useful Intego features include the following:
- Safe Browsing — secures your activity while surfing the web.
- ContentBarrier — protects kids by helping block inappropriate content online.
- Mac Washing Machine — helps optimize system performance.
- Personal Backup — provides safe backup and recovery for important files.
Intego’s plans start as low as $19.99/year and protect up to 5 devices. However, I found that Intego’s Mac Premium Bundle is the best option at $34.99/year. It includes all the app’s features and is worth the slightly increased cost. Plus, you can try Intego without risk with its 30-day money-back guarantee. I got a refund in just 10 days when I tested the refund policy.
5. Bitdefender — Feature-Rich Antivirus That Offers Effective Defense Against Malware
Quick Look: Bitdefender Results
| Security | advanced — 100% malware detection via scans, 100% real-time malware protection, multiple scan types, advanced firewall, ransomware protection, and phishing protection |
| Features | excellent — password manager, built-in VPN, file shredder, parental controls, Safepay browser, and more |
| Native apps | all major platforms — Windows, macOS, iOS, and Android |
| Device connections | up to 10 (depending on the plan) |
| Customer support | 24/7 live chat, phone support, email support, community forums, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons | ✘ VPN is limited to 200MB on plans ✘ more expensive after the first year |
| Best price | $29.99/year — free plan also available |
Bitdefender’s biggest strength is its huge suite of additional features. Additionally, the app is cloud-based to ensure it doesn’t slow down performance and uses innovative machine-learning techniques to identify sophisticated malware. Some of the key features available in Bitdefender include the following:
- Web protection — safeguards against unsafe websites.
- Firewall — protects against network intrusions.
- Parental control suite — helps safeguard your kids’ activity.
- Safepay — provides security during online banking and shopping.
- File Shredder — deletes sensitive files permanently to ensure they’re inaccessible.
- Webcam and microphone protection — blocks unauthorized access to your mic and webcam.
- Password manager — defends passwords and other sensitive credentials.
- Built-in VPN — encrypts your connection and keeps you anonymous online.
- Anti-theft — helps track lost or stolen devices.
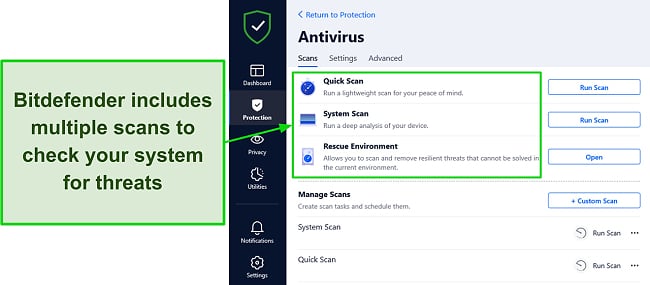
During my tests, Bitdefender’s multiple virus scans delivered impressive results by finding 100% of malware on my system. I also like that Bitdefender has multiple scans, including a useful Rescue Environment scan that reboots your system into safe mode to remove threats that traditional scans can’t.
Bitdefender also provides reliable support via live chat, phone, and email. Plus, it has a detailed knowledge base with lots of helpful information about the app. The quickest way to get help is via the 24/7 live chat, though. The support isn’t as fast as Norton’s, but it’ll still provide the help you need whenever you contact it.
You can get Defender for as low as $29.99/year. However, I consider the $49.99/year Total Security plan a better choice. It offers all the app’s core safety features while also including its anti-theft and optimization tools.
You can also try Bitdefender risk-free, as there’s a 30-day money-back guarantee. I also tested the refund policy via email, and its support confirmed my refund with no questions asked. Afterward, I had the money back in my account in 5 days.
6. Malwarebytes — Offers Well-Rounded Protection on All Platforms
Quick Look: Malwarebytes Results
| Security | great — 99% malware detection via scans, web protection, ransomware protection, and real-time security. |
| Features | average — built-in VPN. |
| Native apps | all main platforms — Windows, macOS, iOS, and Android |
| Device connections | up to 20 (depending on the plan) |
| Customer support | 24/7 live chat, email support, and an online knowledge base. |
| Money-back guarantee | 60 days |
| Minor cons | ✘ VPN is only available on the most premium plan. ✘ doesn’t have a firewall |
| Best price | $44.99/year — free plan also available |
Malwarebytes offers well-rounded safety on Windows, macOS, iOS, and Android devices. It has many safety features, and I was impressed to see that its scans find and remove 99.9% of malware.
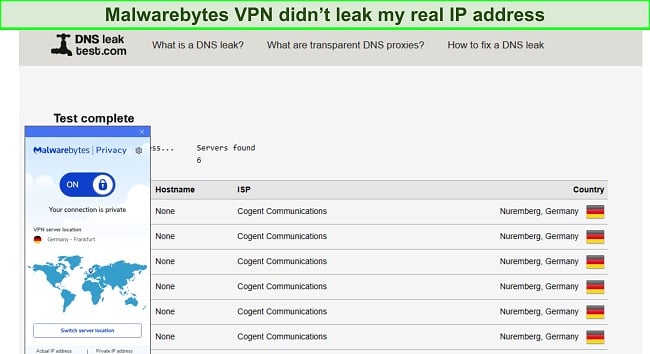
Malwarebytes also finds 99.2% of real-time threats. Plus, it includes a built-in VPN for improved safety online. The VPN uses AES 256-bit encryption and has a strict no-logs policy to ensure your anonymity. During my tests, Malwarebytes’ VPN never leaked my actual IP address when connected.
While it’s missing its own firewall and isn’t as feature-rich as Norton, Malwarebytes has the following to improve security:
- Browser Guard — blocks ads, trackers, and unsafe websites that may infect your device.
- Ransomware protection — stops ransomware infections that could encrypt sensitive data.
Malwarebytes has a free plan, but it only offers on-demand malware scanning, meaning it’s not the best for security. The cheapest plan starts at $44.99/year. However, I suggest you get Malwarebytes’ Plus plan for the best safety, as it includes the VPN and all the other important features.
There’s also a 60-day money-back guarantee that lets you try Malwarebytes without risk. When I asked for a refund via email, the agent confirmed it immediately. I had my money back 8 days later.
7. Panda — Includes Some Unique Security Features for Improved Safety
Quick Look: Panda Results
| Security | great — 98% malware detection via scans, ransomware protection, web protection, and a customizable firewall |
| Features | decent — built-in VPN, anti-theft tools, process monitor, password manager, and parental controls |
| Native apps | all main platforms — Windows, macOS, iOS, and Android |
| Device connections | up to unlimited (depending on the plan) |
| Customer support | 24/7 live chat, phone support, community forums, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons | ✘ VPN capped at 150/MB a day on all plans except 11 ✘ virus scans don’t detect 100% of malware |
| Best price | $23.99/year — free plan also available |
Panda is a solid antivirus with a few unique features that set it apart from other options. Plus, Panda’s malware scanner was very impressive in my tests. It found and removed 98% of malware on my system, meaning it’s good enough to be alongside the best security apps.
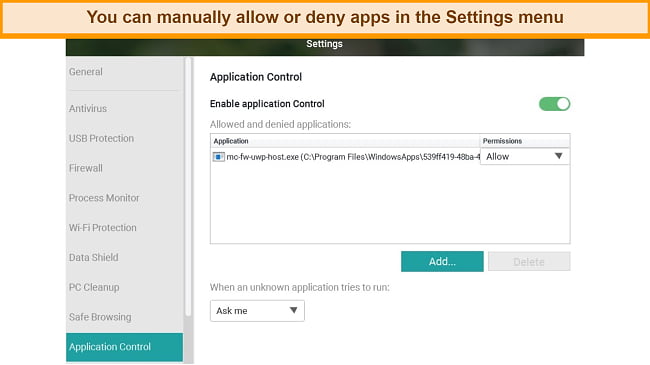
The Application Control function lets you choose exactly what apps can work on your PC, which is an innovative feature that other apps don’t offer. Plus, Panda alerts you if apps try to make unauthorized changes or try to install themselves without your permission.
You’ll also get multiple other features with Panda that improve security. These include the following:
- Rescue Kit — creates a bootable USB drive to recover infected computers.
- Built-in VPN — uses AES 256-bit encryption to safeguard your online activity.
- Anti-theft — helps find and recover lost or stolen devices.
- File encryption — encrypts sensitive files you don’t want others to access.
- WiFi protection — monitors your network and informs you if intruders connect.
Panda’s features are useful, but one downside to this app is that the VPN is limited to 150MB/day on all plans except one. The plans start at $23.99/year, but you should get Panda’s $42.99/year Premium plan, as it includes an unlimited VPN and all the app’s other key safety features. Also, it lets you protect unlimited devices
There’s also a 30-day money-back guarantee that lets you try Panda without risk. If unsatisfied, you can easily get a refund by filling out a web form. When I tested its refund policy, I had my money back in just 8 days.
8. Avira — Solid Antivirus That Only Highlights a Few False Positives
Quick Look: Avira Results
| Security | great — 100% malware detection via scans, real-time protection, ransomware protection, and web protection |
| Features | average — optimization tools, Safe Shopping, built-in VPN, and a password manager |
| Native apps | all main devices — Windows, macOS, iOS, and Android |
| Device connections | up to 5 (depending on the plan) |
| Customer support | email support, phone support, and an online knowledge base |
| Money-back guarantee | 60 days |
| Minor cons | ✘ unreliable customer support ✘ lots of in-app upselling |
| Best price | $26.99/year — free plan also available |
Avira is excellent at detecting malware, as it found 100% of malware via its scans and was equally effective against real-time threats during my tests. I also like that it’s lightweight and doesn’t cause increased slowdown or battery drain. Note that it flags a few false positives, meaning its results aren’t as reliable as Norton’s.
You’ll also get many useful security features in Avira, including the following:
- Built-in VPN — encrypts your connection with AES 256-bit encryption for safety and anonymity.
- Software updater — finds and updates any outdated apps to fix vulnerabilities.
- Password manager — offers secure storage for passwords and other sensitive data.
- Hyper Boost — makes optimizations to help your system boot faster.
- Power Cleaner — removes junk files to free up space on your system.
Avira’s Phantom VPN lets you connect unlimited devices and delivers reliable overall performance. It maintained decent connection speeds and never leaked my actual IP address, even after multiple leak tests.
You can get Avira’s free plan for basic security, and its paid plans start at just $26.99/year. Avira’s $59.99/year Prime plan delivers the best value, though. It offers all the app’s key features and protects up to 5 devices. Whichever plan you choose, you can try Avira risk-free for 60 days with its money-back guarantee and ask for a refund if you aren’t satisfied.
9. AVG — Comes With Multiple Features to Defend Against Cyber Threats
Quick Look: AVG Results
| Security | great — 100% malware detection via scans, secure firewall, ransomware protection, web protection, and more |
| Features | decent — Anti-track, built-in VPN, optimization tools, and a data shredder |
| Native apps | all main devices — Windows, macOS, iOS, and Android |
| Device connections | up to 10 |
| Customer support | 24/7 live chat, community forums, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons | ✘ past privacy concerns ✘ paid plans cost more than other top choices |
| Best price | $59.98/year — free plan also available |
Despite privacy issues harming its reputation in the past, AVG has been redeeming itself well and is now considered a reliable antivirus. With multiple security features and impressive malware detection scores, I consider AVG a good antivirus for protecting all your devices.
In my tests, AVG reliably found and removed malware from my system with a 100% detection score. I also like that its real-time security is just as effective and stops any cyber threats before they infect your device. Plus, AVG’s advanced firewall has features like leak protection, ARP spoofing alerts, and port scan alerts for improved safety.
- Built-in VPN — uses AES 256-bit encryption to secure your online activity.
- Ransomware protection — stops ransomware from modifying files on your system.
- Anti-track — blocks trackers from monitoring your activity for advertising purposes.
- Data Shredder — shreds and permanently removes sensitive files to ensure they’re inaccessible.
- TuneUp — deletes junk files and helps optimize system performance.
- Web protection — blocks malicious websites and checks your emails for malware.
- Hack Alerts — informs about any compromised accounts you have.
AVG has a free plan, but it only offers basic protection. Its cheapest paid offering is the $59.88/year Internet Security plan, but you should get the $51.99 Ultimate plan for the best value. It includes every important safety feature and is worth the slightly increased cost. Note that AVG costs more than other options on this list, including top choices like Norton.
Whichever plan you choose, AVG’s 30-day money-back guarantee lets you try it risk-free. It’s easy to claim a refund if you’re unsatisfied, and I had my money back in just 2 days when I requested mine via live chat.
10. Avast — Pairs Solid Malware Detection Scores With Various Impressive Features
Quick Look: Avast Results
| Security | great — 100% malware detection via scans, multiple real-time security shields, built-in firewall, web protection, and more |
| Features | great— built-in VPN, optimization tools, hack alerts, sandbox, webcam shield, and more |
| Native apps | all main devices — Windows, macOS, iOS, and Android |
| Device connections | up to 10 |
| Customer support | 24/7 live chat, phone support, email support, community forums, and an online knowledge base |
| Money-back guarantee | 30 days |
| Minor cons | ✘ the free plan only offers basic protection ✘ customer support is slow to respond |
| Best price | $49.99 — free plan also available |
Avast is a solid overall antivirus that’s been redeeming its reputation ever since it sold its data-selling subsidiary. It ensures safety on Windows, macOS, iOS, and Android devices with various security tools, including the following:
- Sandbox — provides an isolated environment to run and check potentially unsafe apps.
- Advanced firewall — prevents network intrusion with multiple advanced safety features.
- Bank mode — offers a safe way to shop and bank online safely.
- Secure browser — blocks ads and trackers while surfing the web.
- Webcam Shield — stops unauthorized webcam access.
- Cleanup Premium — optimizes system performance and removes junk files.
During my tests, Avast showed strong malware removal capabilities by finding and removing 100% of malware on my test system. Also, it has web, ransomware, behavior, and mail shields for enhanced real-time protection.
While it offers reliable security, Avast’s support can be very slow. Live chat can sometimes take over 5 minutes to find an agent, and the email support took more than 2 days to answer my ticket. Thankfully, the agents are knowledgeable, and the answers you get will be very helpful.
Avast has a basic free plan, but it’s not reliable for comprehensive security. You should get Avast’s $79.99 Ultimate plan if you want the best value and protection. Also, there’s a 30-day money-back guarantee that lets you try Avast without risk. If unsatisfied, you can request a refund via the web portal and get your money refunded.
Comparison Table: 2024’s Best Antivirus Software
| Malware Detection via Scans | Firewall | Built-in VPN | Number of Devices | Lowest Price | Money-Back Guarantee | |
| 1. Norton | 100% | ✔ | ✔ | unlimited | $29.99 | 60 days |
| 2. TotalAV | 100% | ✘ | ✔ | 6 | $19.00 | 30 days |
| 3. McAfee | 100% | ✔ | ✔ | 10 | $39.99 | 30 days |
| 4. Intego | 99.4% | ✔ | ✘ | 5 | $19.99 | 30 days |
| 5. Bitdefender | 100% | ✔ | ✔ | 10 | $29.99 | 30 days |
| 6. Malwarebytes | 99% | ✘ | ✔ | 5 | $44.99 | 30 days |
| 7. Panda | 98% | ✔ | ✔ | unlimited | $23.99 | 30 days |
| 8. Avira | 100% | ✘ | ✔ | 5 | $26.99 | 60 days |
| 9. AVG | 100% | ✔ | ✔ | 10 | $59.98 | 30 days |
| 10. Avast | 100% | ✔ | ✔ | 10 | $49.99 | 30 days |
Warning! Avoid These 2 Antivirus Brands
1. Microsoft Defender
Microsoft Defender is decent for basic security, but it’s missing features like a customizable firewall, VPN, or password manager. You get all these features with the top premium antiviruses, meaning Microsoft Defender doesn’t provide the top-quality security they do.
2. Trend Micro
Trend Micro is generally good, as it has good malware detection scores and multiple safety features. However, I found during tests that Trend Micro sometimes fails to find Trojans, meaning it’s not the best choice for well-rounded safety.
How to Choose the Best Antivirus for Your Operating Systems
Norton stands out as the top antivirus for Windows, offering perfect malware detection, reliable security features, and excellent customer support.
Intego proves to be the optimal antivirus solution for macOS, offering perfect detection scores against Mac-specific threats and many security features.
Norton’s Android app shines with robust malware scanning, a built-in VPN, and WiFi protection, making it an ideal choice for securing Android devices.
McAfee’s iOS app, despite the inherent security of iOS devices, adds an extra layer with features like web protection and anti-theft capabilities.
How I Tested and Ranked the Top Antivirus Software in 2024
I used the following criteria to determine 2024’s best antiviruses:
- Powerful antivirus engine — I chose antiviruses that reliably remove threats with perfect (or near-perfect) malware detection scores.
- No (or few) false positives — I picked security apps that flag no (or very few) false positives, as these can be annoying.
- Useful extra features — I found apps with extra features like built-in VPNs, password managers, and more for improved protection.
- Performance impact — I selected antiviruses that don’t slow down device performance or cause increased battery drain.
- Ease of use — I chose antiviruses with beginner-friendly apps that anyone can easily use.
- Customer support — I picked antiviruses that offer responsive customer support through multiple channels.
- Value for money — I prioritized security apps with affordable price plans that are worth the cost.
- Money-back guarantee — I only chose antiviruses with money-back guarantees that let you test them risk-free.
Free vs Paid Antiviruses: Advantages & Risks
Differences Between Free and Paid Antiviruses
While free options provide a basic level of protection, top premium alternatives often offer advanced security and comprehensive feature sets. You can expect the following differences between free and paid antivirus apps:
Security
- Free: Basic protection against common threats through on-demand malware scanning.
- Paid: Comprehensive security against all malware through advanced features like real-time protection, firewall, and secure browsing.
Additional Features
- Free: Few or no extra features.
- Paid: Additional layers of security through ransomware protection, built-in VPN, password manager, and more.
Updates and Support
- Free: Limited or delayed updates; minimal customer support.
- Paid: Regular updates and dedicated customer support for prompt assistance.
Ads
- Free: Many distracting ads and upsells in the interface.
- Paid: Clean and easy-to-use interface without any annoying ads.
Risks of Using Free Antiviruses
Besides the obvious security difference between free and paid apps, there are also multiple risks to using free antiviruses. Some of the significant risks include the following:
- Ads and pop-ups. Free antiviruses often have many intrusive ads and pop-ups that make them harder to use.
- Data collection concerns. Free antiviruses may collect your user data for marketing purposes.
- Less effective against advanced threats. These apps don’t always have advanced features like ransomware protection and customizable firewalls to defend against sophisticated malware.
- No priority support. Customer support is generally slower for free antiviruses, meaning it can take a while before you get help with issues.
What Is the Best Antivirus According to Reddit Users?
Reddit can be a reliable resource for antivirus recommendations. This happens because people who’ve used these apps for a long time give tips based on their own years of experience. I found that the following antiviruses were among Reddit’s most popular recommendations:
- Norton: Considered by many Redditors as the #1 antivirus because of its variety of security features.
- Malwarebytes: Redditors credit Malwarebytes’ lightweight design as the key reason they prefer it. It never causes increased battery drain or slowdowns.
- Avira: Many people on Reddit recommend Avira, as it has one of the best free plans available in an antivirus.
What Cyber Threats Can the Best Antiviruses Protect You From?
Investing in an advanced premium antivirus helps safeguard your devices against almost all sophisticated cyber threats. Here’s a breakdown of the threats these antiviruses can protect against:
- Adware: Top antiviruses can reliably detect and remove adware from your device to ensure you aren’t constantly served with unnecessary ads.
- Phishing attacks: With advanced phishing detection capabilities, these antiviruses can identify and block attempts to trick users into revealing sensitive information, mitigating the risk of falling victim to phishing attacks.
- Spyware: The best antiviruses proactively detect and remove spyware, preventing unauthorized access to your sensitive data.
- Potentially unwanted programs (PUPs): Antiviruses can identify and eliminate PUPs, ensuring that unwanted software doesn’t compromise your system’s performance or security.
- Trojans: Premium antiviruses offer robust protection against Trojans, blocking their malicious activities and preventing unauthorized access to your system.
- Ransomware: Advanced features in these antiviruses actively defend against ransomware, safeguarding your files and preventing extortion attempts.
- Rootkits: Top premium antiviruses can detect and remove rootkits, protecting the integrity of your system by preventing stealthy, unauthorized access.
- Worms: Worms can go unnoticed and spread throughout your system to corrupt important files. The best antiviruses are equipped to identify and eliminate worm threats, preventing their propagation and potential damage to your system.
FAQs: Antivirus Software in 2024
Why do I need antivirus software in 2024?
You need a top antivirus app to safeguard yourself against sophisticated cyber threats that are evolving every day. A single phishing scam or dangerous file download is all it takes to compromise your devices and privacy nowadays. So, you must ensure you have reliable antivirus software to stop this.
Isn’t the included antivirus on my device enough?
While built-in antiviruses like Microsoft Defender are enough for basic security, they don’t offer advanced safety features like the best antiviruses. Also, their malware detection scores aren’t as impressive, nor do they have reliable customer support you can contact whenever you face issues.
What is the best antivirus software for Mac?
Intego is the best antivirus you can get for Mac. It’s designed specifically for macOS and reliably detects malware via its scans. Plus, it has excellent real-time protection, an innovative firewall, and other advanced protection features to ensure your devices are protected.
What is the best free antivirus program?
Avira is the best free antivirus available. Many apps offer free plans, but Avira includes its reliable virus scanner and real-time security completely free. You won’t get tools like the unlimited VPN and other advanced safety features in the free plan, but I found that Avira is better than most other free antiviruses.
What is the overall best antivirus of 2024?
Norton is the best overall antivirus you can get this year. It has a flawless 100% malware detection score via scans, and it’s equally effective against real-time threats. Plus, Norton has advanced features like a customizable firewall, built-in VPN, web protection, parental controls, and more to ensure you’re protected in every way.
How does an antivirus work?
The best antiviruses scan your device for malware like viruses, keyloggers, ransomware, and more. These antiviruses use a database of verified malware signatures that they compare your files against to check for malware. Also, top modern-day antiviruses use machine learning to analyze a file’s behavior to check if it’s malicious.
Secure All Your Devices Using the Best Antivirus
In conclusion, getting a top premium antivirus is critical for safety. Otherwise, your devices are still at risk of getting infected by sophisticated malware despite the built-in security features of modern operating systems.
All the security apps I’ve listed above offer excellent protection against sophisticated malware and other modern cyber threats. They have impressive malware detection scores and additional features like firewalls, built-in VPNs, and more to improve security.
While each of my top antiviruses is effective, I consider Norton the #1 antivirus in 2024. Its flawless 100% malware detection, customizable firewall, worthwhile pricing, and responsive customer support make it an excellent choice. Plus, the 60-day money-back guarantee means you can try Norton without risk.